technology
Installing VMware Workstation Pro 26H1
Here are the steps I took to install VMware Workstation Pro 26H1.
Meet the requirements
The number one issue why Workstation doesn’t install is failure to read the requirements. Ensure your hardware and your BIOS settings meet the requirements prior to installation.
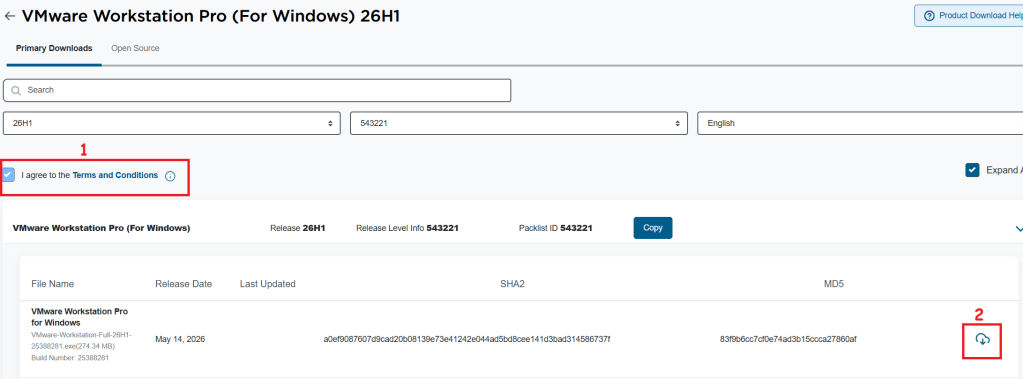
Download Workstation
I’ll need to download VMware Workstation Pro 26H1. The good news is, it’s free and users can download it at the Broadcom support portal. Once you log in, you can find it under the downloads section under FREE Downloads. Need more guidance on the portal, see this KB.
Note: Make sure you click on the ‘Terms and Conditions’ plus the check box (1) before you click on the download icon (2).
Windows Settings
Disable Windows Virtualization Settings
If you are deploying Workstation on to Windows the disablement of Hyper-V and Device Guard conflicts are important. Basically, Workstation needs these to be disabled to achieve optimal performance plus support nesting. If they are not disabled the following error will appear during the installation of Workstation.
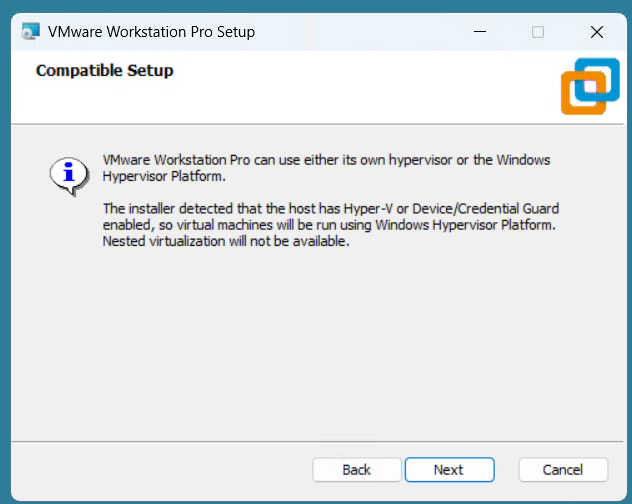
Note: Before starting, I create a current Windows restore point prior to making the following changes.
To resolve this, I used the Microsoft Device Guard and Credential Guard Hardware Readiness Tool.
- Download the Device Guard and Credential Guard hardware readiness tool from Microsoft.
- Extract the downloaded ZIP file.
- Use the tool to disable Device Guard and Credential Guard:
- Open PowerShell window as an administrator.
- Navigate to the folder where you extracted the tool.
- First run this command to get Execution Policy:
- Set-ExecutionPolicy Unrestricted -Scope Process
- Now run the script with the -Disable parameter to disable Device and Credential Guard
- DG_Readiness_Tool_v3.6.ps1 -Disable
- Reboot your computer.
- During the boot process, Windows will ask you to confirm the changes. Follow the on-screen instructions to proceed (Just press F3).
- When complete your computer will reboot.
Workstation Installation
Launch the Workstation program and when prompted click Next.
Check Accept and Click Next.
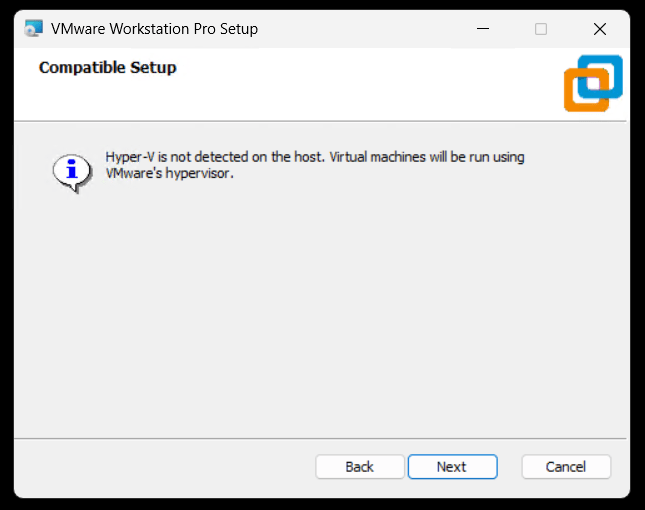
Ensure VMs are running on VMware Hypervisor.
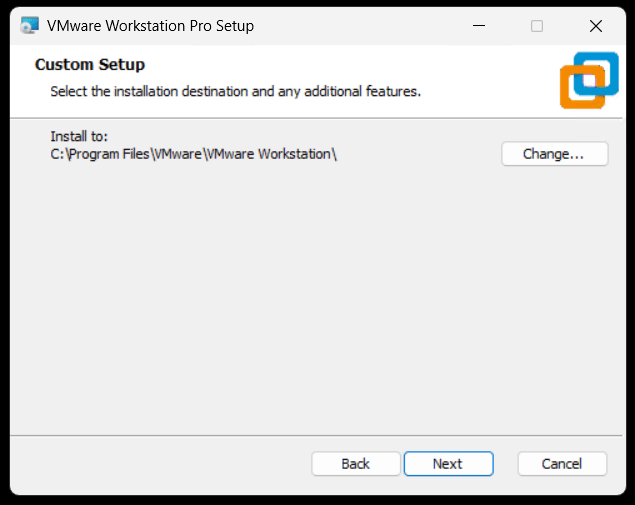
Ensure directory is correct and click next.
Click next to accept auto updates and joining the CEIP program.
Click next to create shortcuts.
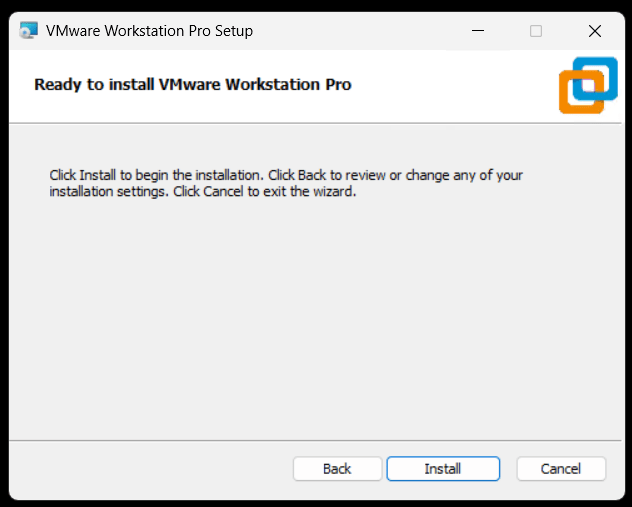
Click Install to install Workstation.
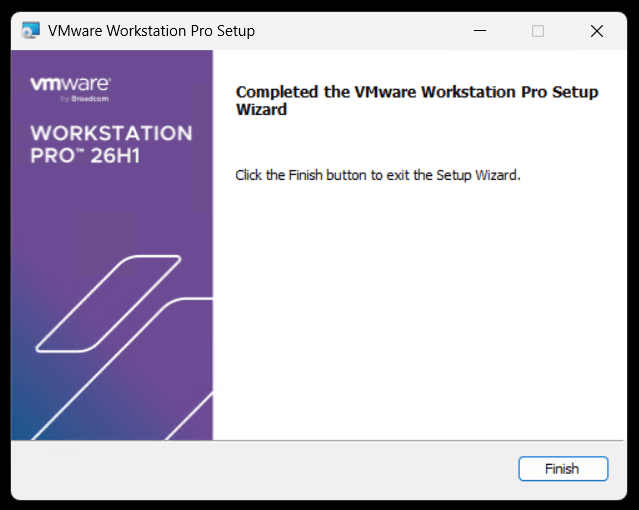
Allow the installer to complete and click Finish to finalize.
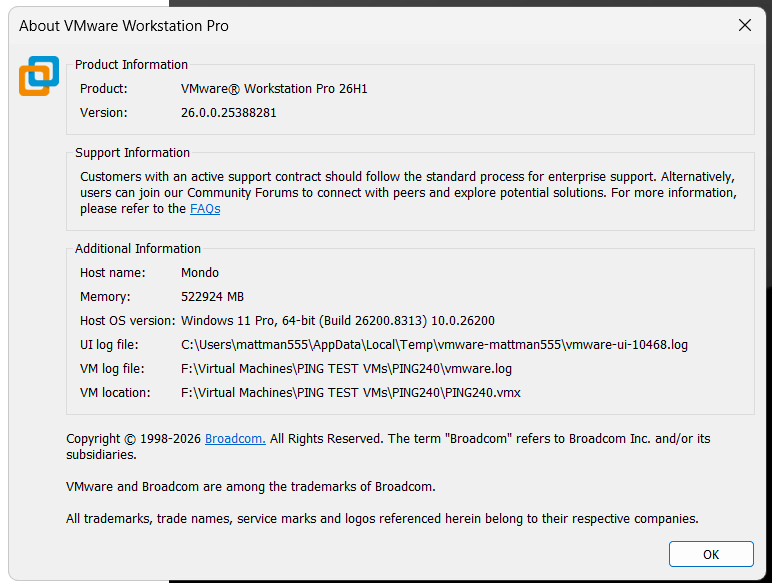
Open Workstation > Help > about to to validate install.
VMware Workstation Pro 26H1 is here and, its got a 64-Bit upgrade!!
The latest update to VMware Workstation Pro, version 26H1, has officially arrived! Whether you are a developer, a sysadmin, or a tech enthusiast, this release brings a host of updates designed to streamline your virtualization workflow and expand compatibility with the latest operating systems.
Personally, I’m excited to try out is new added support for 64-Bit applications/binaries.
What’s New
- VMware Workstation Pro 26H1 contains security and bug fixes.
- Added support for 64-Bit VMware Workstation Pro for Windows: VMware Workstation Pro for Windows is now available as a 64-bit application and all binaries, libraries, installer components, and related services are delivered and executed as 64-bit processes.
- Recording and reporting time stamps: You can easily identify virtual machines virtual machines by creation and last powered-on time stamp.
- Added support for remote connections to ARM-based ESX hosts, enabling basic virtual machine operations.
- Displaying virtual machine notes in folder tabs.
- Updated the saved credential format: You can easily identify encrypted virtual machines and remote server in the credential manager of the host platform.
- Added support for guest operating systems.
- Guest operating systems
- Ubuntu 26.04 LTS
- Fedora 43
- Fedora 44
- SUSE Linux Enterprise 16
- openSUSE 16.0
- FreeBSD 15.0
- Guest operating systems
- Added support for Host operating systems
- Ubuntu 26.04 LTS
- Fedora 43
- Fedora 44
- SUSE Linux Enterprise 16 GA
- openSUSE 16.0
Reminder: Workstation Pro is Now Free!
In case you missed the recent shift, VMware Workstation Pro is now free for personal, commercial, and educational use. You no longer need a license key to unlock the full power of the industry-standard desktop hypervisor. Just download, install, and start building.
Final Thoughts
The 26H1 release is a solid step forward, focusing on the “latest and greatest” in the OS world while giving power users better tools for customization. If you haven’t updated yet, now is the time to head over to the Broadcom Support Portal and grab the latest build.
Ready to upgrade? Check out the full technical details and resolved issues list in the official release notes.
VMware Cloud Foundation 9.1 (VCF 9.1) key events, webinars, and Resources
Below is a summary of some of the great announcements around the VCF 9.1 release.
Discover What’s New in VCF 9.1
Watch this recording to see the new features in action through demo-walkthroughs and discover how the newly announced partnerships will expand VCF 9.1 capabilities.
Modules:
- The New Era of Virtualization: AI-ready Private Cloud
- Solving the AI Memory Crisis with VMware Cloud Foundation
- Exploring VCF 9.1: Private AI and Memory Tiering Insights
- VMware Advanced Cyber Compliance: Bridging the Resilience Gap
Learn More
- VMUG Global Event (June 25th)
- Meet our Experts Register for VMware Explore 2026 (Aug 31 – Sep 3)
- Level Up Get Certified on VCF 9.1
Strategic Roadmap & Training
The following schedule outlines key opportunities to engage with VCF experts and the broader Broadcom ecosystem in 2026. The marquee event, VMware Explore 2026, returns to Las Vegas in late August.
| Date | Event / Webinar Name | Location / Type |
|---|---|---|
| May 5, 2026 | Broadcom’s VMware in 2026: VCF 9, Containers, and AI | Webinar (On-Demand) |
| May 13-15, 2026 | VCF Experience Day (Hosted by TD SYNNEX) | Dallas/Plano, TX |
| Aug 31 – Sep 3, 2026 | VMware Explore 2026 Las Vegas | Las Vegas, NV |
| Sep 29-30, 2026 | VMware Explore on Tour: Mumbai | Mumbai, India |
| Oct 1-2, 2026 | VMware Explore on Tour: Singapore | Singapore |
| Oct 13-14, 2026 | VMware Explore on Tour: Frankfurt | Frankfurt, Germany |
Virtually Speaking Podcast Series and others
Hosted by Pete Flecha and John Nicholson, the Virtually Speaking Podcast provides weekly technical deep dives into the VCF 9.1 ecosystem. The new “VCF 9 Core” series features product engineers explaining the architectural changes.
| Episode 1: Introducing VCF 9.1: Built for Efficiency and Resilience | Episode 6: VCF 9.1: From AI Hype to Production Reality |
| Episode 2: From Infrastructure to Innovation: VCF 9.1 Core Explained | Episode 7: VCF 9.1: Scaling Secure Edge Deployments |
| Episode 3: VCF 9.1: Automation, Kubernetes APIs, and Faster Deployments | Episode 8: VCF 9.1 Cyber Resilience: From Attack to Recovery with Confidence |
| Episode 4: Inside VCF 9.1: Platform, Lifecycle, and What’s Different Now | Episode 9: Designing VCF 9.1: Architecture, Sizing, and Scale in Practice |
| Episode 5: From Rising Costs to Smarter Storage: The VCF 9.1 Reality |
Resources & Documentation
Critical Reference Materials
- Product News Release: Broadcom Announces VMware Cloud Foundation 9.1
- Broadcom TechDocs: TechDocs have been completed updated making it easier to find content.
- Release Notes: The full VCF 9.1 Release Notes detail the specific upgrade paths from VCF 5.x.
- VCF Import Guide: Technical documentation on how to prepare brownfield vSphere clusters for ingestion.
- Private AI Reference Architecture: A comprehensive guide on sizing GPU clusters and configuring vSAN ESA for high-throughput AI training.
Tech Blogs
- Announcing VCF 9.1: Modern Private Cloud Built for Efficiency and Resilience
- Scale Smarter, Save More: Redefining Infrastructure Economics with vSphere in VCF 9.1
- Announcing VCF Edge 9.1 A Scalable, Autonomous Edge Platform
- Continuous Compliance, Integrated Cyber Recovery and Enhanced Platform Security for VCF 9.1
- Streamline, Simplify and Protect all your AI workloads with VCF 9.1
- VCF Professional Services and Lifecycle Support Solution Brief
Coming Soon
HOL
- Test-Drive VCF 9.1 and more for free
- What’s New in VCF 9.1
- Memory Tiering in VCF 9.1
- Native Kubernetes Workloads on VCF 9.1
Solution Architecture Guides
- Self-Service Multi-tenant Private Cloud Consumption
- Private AI Service Deployment and Consumption with VCF 9.1
- VCF Edge Design for Retail, Manufacturing
- Flexible Storage Deployment Models
Next Steps
For organizations planning their upgrade path, the immediate next step is to audit current hardware compatibility against the VCF 9.1 HCL (Hardware Compatibility List), particularly if planning to leverage the new NVMe memory tiering capabilities.
REF: See the follow URL for more updates. https://go-vmware.broadcom.com/whats-new-in-vcf
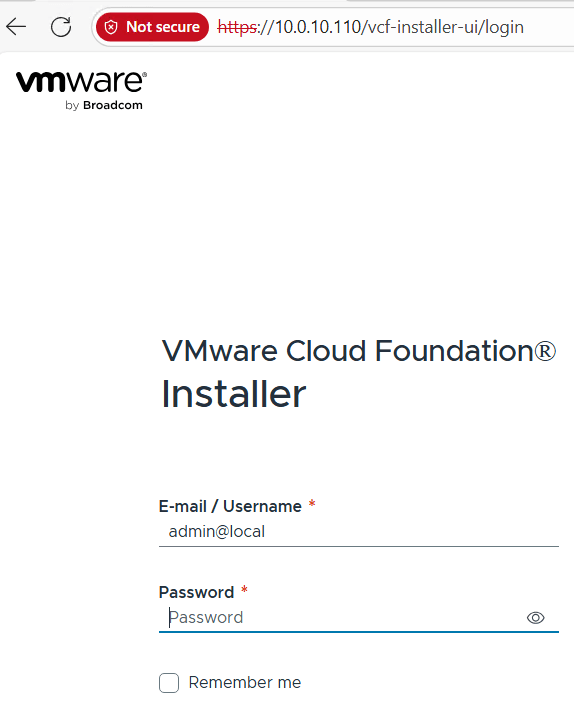
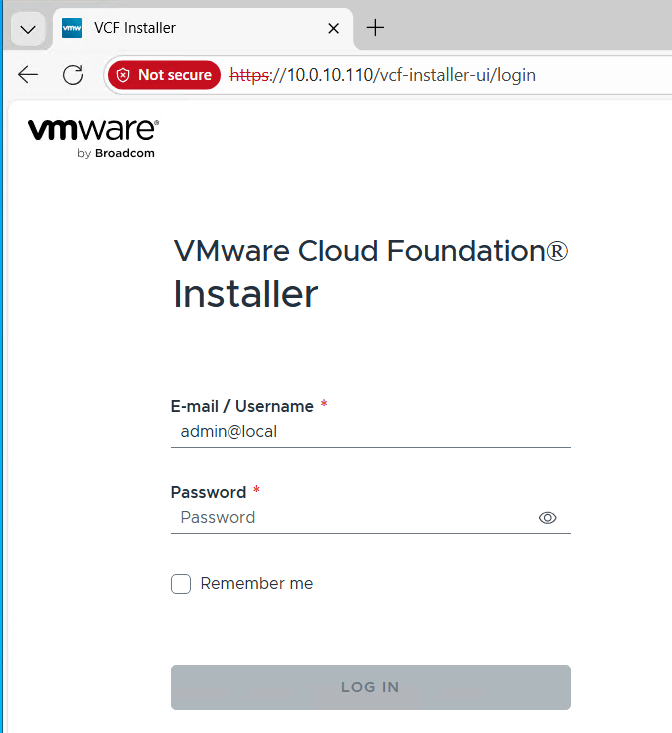
Managing the SDDC Installer admin@local Account – Password Resets and lockouts
We’ve all been there. We deploy an appliance and then we can’t find the password. We try to log in a few times and the accout gets locked out. For administrators managing VMware Cloud Foundation (VCF), the admin@local account is a critical account. Introduced to provide access to the SDDC Manager APIs and the VCF Installer even when the management vCenter Server or Identity Provider (SSO) is unavailable, it ensures you aren’t locked out of your environment during critical failures.
Phase 1: Resetting the Forgotten Password
If you don’t know the current password, you must manually inject a new one via the SDDC Manager console. This process involves creating a secure credential file and hashing your new password using OpenSSL.
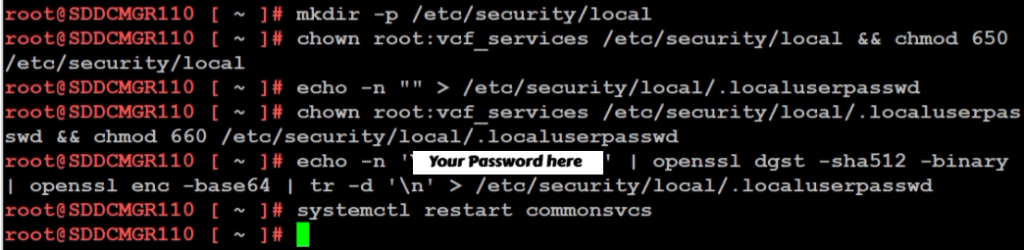
According to KB 403099, follow these steps on the SDDC Manager VM:
- Access the Console: Log in to the SDDC Manager via SSH as the
vcfuser, then switch to root:su -or simply logon as root. - Initialize the Security Directory: Ensure the local security directory exists with the correct permissions:
mkdir -p /etc/security/local chown root:vcf_services /etc/security/local && chmod 650 /etc/security/local - Create the Password File: Create an empty file to house the secret:
echo -n "" > /etc/security/local/.localuserpasswd chown root:vcf_services /etc/security/local/.localuserpasswd && chmod 660 /etc/security/local/.localuserpasswd - Generate the New Password: Replace
You Password herein the command below with a password that meets the VCF requirements (12-127 characters, including uppercase, lowercase, numbers, and special characters):echo -n 'Your Password Here' | openssl dgst -sha512 -binary | openssl enc -base64 | tr -d '\n' > /etc/security/local/.localuserpasswd - Restart Services: Apply the change by restarting the SDDC Manager services:
/opt/vmware/vcf/operationsmanager/scripts/cli/sddcmanager_restart_services.sh
Phase 2: Unlocking the Account
Even with a fresh password, if the account was previously locked due to too many failed attempts, the system may still reject your login. You must now clear the lockout state.
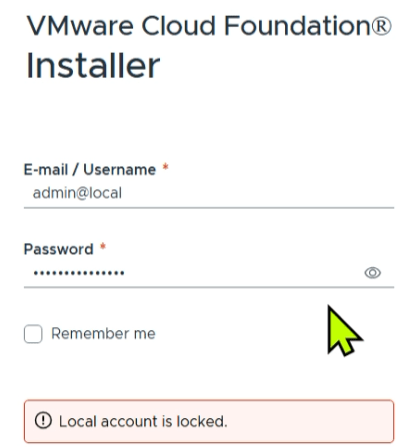
Based on KB 403316, you can clear the lockout by restarting the common services component:
- Stay in the Console: From your existing
rootsession on the appliance (or via the VCF Installer appliance if that is where the lockout occurred). - Clear the Lockout: Run the following command to restart the service responsible for authentication:
systemctl restart commonsvcs - Final Verification: Wait a moment for the service to initialize, then attempt to log in to the web interface using the new password you created in Phase 1.
Summary
When you are locked out of your VCF environment and have forgotten your credentials, the path to recovery is a two-step process. By first following KB 403099 to manually reset the password via the command line, and then following KB 403316 to restart the commonsvcs and clear the lockout, you can regain control of your SDDC Manager and VCF Installer.
GL.iNet Comet (GL-RM1) a handy single KVM Over IP
Recently I was working on my Ubuntu 25 workstation and I needed a way to reliably remote into the system. This Workstation uses a Supermicro motherboard. It has built in IPMI (remove KVM) but the it only supports remote KVM to the on board video card. xrdp was other option but it is no longer supported under Ubuntu 25. Using Microsoft RDP to Ubuntu desktop or remote sharing constantly disconnected, had issues, or would show black screens. The VNC options I looked at were either buggy or had a subscription fee. Other options like Team Viewer, and No Machine either cost too much or simply were too complex.
Enter the GL.iNet Comet (GL-RM1) It is a specialized hardware-based KVM-over-IP (Keyboard, Video, Mouse) device designed to give you complete remote control over a computer event at the BIOS level. Unlike software solutions, the Comet allows you to access a machine even if the operating system has crashed or hasn’t booted yet.
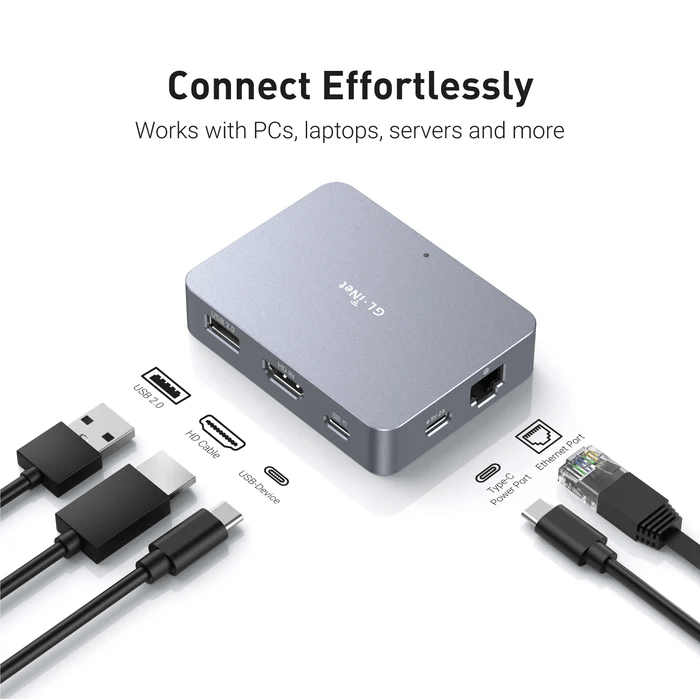
Key Features
| Feature | Specification |
|---|---|
| Max Resolution | 4K @ 30fps (also supports 2K @ 60fps) |
| Processor | Quad-core ARM Cortex-A7 |
| Memory / Storage | 1GB DDR3L RAM / 8GB eMMC Storage |
| Connectivity | 1x Gigabit Ethernet port (No built-in Wi-Fi) |
| Remote Access | Tailscale integration, GoodCloud, and local web UI |
| Ports | HDMI In, USB-C (Keyboard/Mouse), USB 2.0 (Expansion) |
| Dimensions | 80 x 60 x 17.5mm; 85g |
What I like and don’t like about it:
Pros
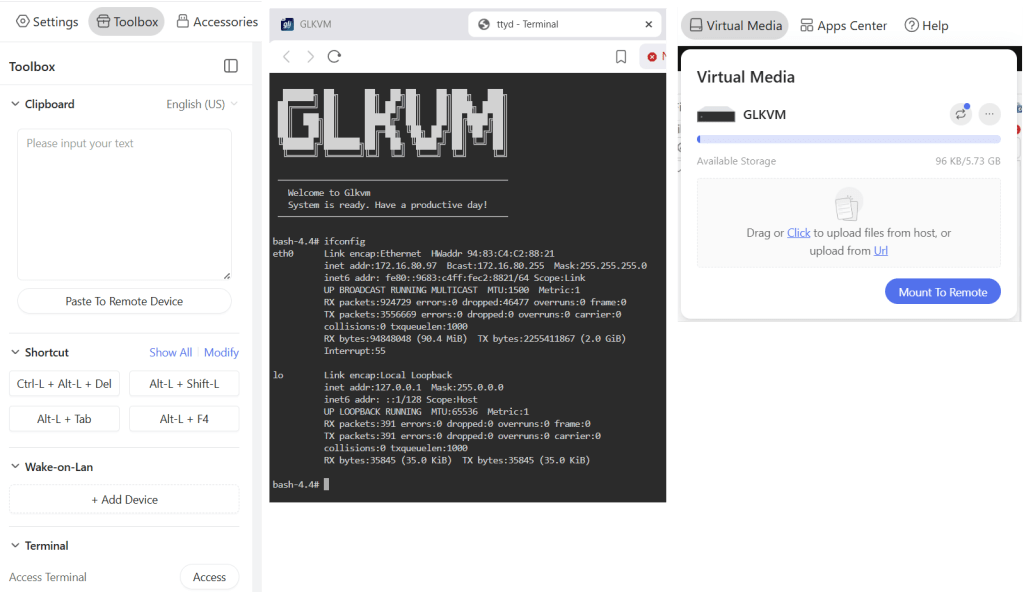
- Feature Rich: For a “budget” KVM over IP the amount of well laid out features and settings is a huge plus.
- BIOS-Level Access: It’s nice to have full control over the workstation. I can remotely troubleshoot a PC before the OS loads, allowing for remote OS installations and BIOS setting changes.
- Ease of Setup: Once I found its IP on my network it was very simple to set up. The web interface is designed very well and works great.
- Toolbox feature: (Fig-1): The Clipboard allows for pasted text to be pasted into a remote device. It also has keyboard shortcuts, WOL, and Terminal access
- Virtual Media and Accessories (Fig-1): It has ~5.5GB of built in storage to mount to the remote host or via the Accessories I can mount a USB memory stick.
- Compact Design: Roughly the size of a computer mouse, making it highly portable for field technicians.
- Mouse Jiggle: Has a feature to enable mouse jiggle on the remote system to keep the remote desktop from locking.
- Remote Cloud Access: I have not tried this feature but you can set it up to be accessed over the internet.
Cons
- No Built-in Wi-Fi: The standard GL-RM1 requires a wired Ethernet connection for internet access.
- USB 2.0 Only: The expansion port is limited to USB 2.0 speeds, which may be slow for large virtual media transfers.
- Power Requirements: It cannot be powered by some PD (Power Delivery) adapters and requires a standard 5V/2A source.
- Limited High-Speed Video: While it supports 4K, it is capped at 30fps, which is sufficient for productivity but not ideal for gaming or smooth video playback.
What could be better:
- Video Display: The initial video display looks a bit pixelated, but with a few video quality changes it works well. It’s totally usable but even in lossless mode it could be a bit more clear.
- The ESC Key: To exit the remote screen you have to push the ESC key or hold the ESC key to exit full screen. Sometimes this ESC key is registered by the remote system and can cause unexpected behaviors. Example – Press ESC and your current window closes out. A work around I found with Windows was to press ALT + TAB and it releases the mouse back to the local OS.
- Mouse Movement: Initially there are two mouse icons (local and remote) and a bit of a delay between them. A few changes in the mouse settings and the experience is much better. Would rather see these be the default settings. Mouse speed is a bit slow, a simple adjustment to the OS mouse speed is helpful.
- High CPU: when running HTML interface in Chrome I notice my laptop fan start up and Chrome uses a lot of RAM. I simply switched to the Brave browser and it works great. Could be something about my setup and Chrome.
How It Compares
The GL.iNet Comet occupies a unique “budget-friendly” tier in the IP-KVM market.
- Vs. PiKVM: While the PiKVM is highly expandable and open-source, it often requires buying a Raspberry Pi separately and assembling it, which can end up being more expensive and bulkier. The Comet is a “plug-and-play” alternative that is significantly cheaper as a complete package.
- Vs. JetKVM: The JetKVM includes a local display for easier on-site monitoring, whereas the Comet is more minimalist. However, users have noted that the Comet’s availability and stability for remote connections (via GoodCloud/Tailscale) make it a very competitive choice.
- Vs. Comet PoE (GL-RM1PE): The PoE variant is slightly larger but allows you to power the device and provide data through a single cable, which is a major advantage for clean server rack setups.
Summing it up
The Comet (GL-RM1) is working out well for my home lab as I needed reliable remote access into my workstation. To me, its primary advantage is providing a reliable, cost effective, feature rich, and quick way to do remote access with out having to install and maintain buggy software based remote access.
VMware Workstation Gen 9: FAQs
I complied a list of frequently asked questions (FAQs) around my Gen 9 Workstation build. I’ll be updating it from time to time but do feel free to reach out if you have additional questions.
Last Update: 03/31/2026
General FAQs
Why Generation 9? Starting with the Gen 7 build, the Gen Number aligns to the version of vSphere it was designed for. So, Gen 9 = VCF 9. It also helps my readers to track the Generations that interests them the most.
Why are you running Workstation vs. dedicated ESX servers? I’m pivoting my home lab strategy. I’ve moved from a complex multi-server setup to a streamlined, single-host configuration using VMware Workstation. Managing multiple hosts, though it gives real world experience, wasn’t meeting my needs when it came to quick system recovery or testing different software versions. With Workstation, I can run/deploy multiple types of home labs and do simple backup/recovery, plus Workstation’s snapshot manager allow me to roll back labs quite quickly. I find Workstation more adaptable, and making my lab time about learning rather than maintenance.
What are your goals with Gen 9? To develop and build a platform that is able to run the stack of VCF 9 product for Home Lab use. See Gen 9 Part 1 for more information on goals.
Where can I find your Gen 9 Workstation Build series? All of my most popular content, including the Gen 9 Workstation builds can be found under Best of VMX.
What version of Workstation are you using? Currently, VMware Workstation 25H2, this may change over time see my Home Lab BOM for more details.
How performant is running VCF 9 on Workstation? In my testing I’ve had adequate success with a simple VCF install on BOM1. Clicks through out the various applications didn’t seem to lag. I plan to expand to a full VCF install under BOM2 and will do some performance testing soon.
What core services are needed to support this VCF Deployment? Core Services are supplied via Windows Server. They include AD, DNS, NTP, RAS, and DHCP. DNS, NTP, and RAS being the most important.
BOM FAQs
Where can I find your Bill of Materials (BOM)? See my Home Lab BOM page.
Why 2 BOMs for Gen 9? Initially, I started with the hardware I had, this became BOM1. It worked perfectly for a simple VCF install. Eventually, I needed to expand my RAM to support the entire VCF stack. I had 32GB DDR4 modules on hand but the BOM1 motherboard was fully populated. It was less expensive to buy a motherboard that had enough RAM slots plus I could add in a 2nd CPU. This upgrade became BOM2. Additionally, blogging about 2 BOMs gives my readers some ideas of different configurations that might work for them.
What topics does the BOM1 Series cover? The BOM1 series provides a comprehensive, step-by-step guide for deploying VMware Cloud Foundation (VCF) 9.0.1 in a nested lab environment. The series covers the full lifecycle, including initial planning and requirements (Part 1), the use of templates (Part 2), and setting up essential core network services (Part 3). Subsequent steps detail the deployment of ESX hosts (Part 4) and configuring the VCF installer with necessary VLAN segmentation (Part 5). To optimize the setup, the guide covers creating an offline repository for VCF components (Part 6), followed by the deployment of VCF 9.0.1 (Part 7).
Finally, the series outlines critical “day-two” operations, such as licensing the environment (Part 8) and managing the proper shutdown and startup procedures for the nested infrastructure (Part 9). This approach creates a fully functional, reproducible lab for testing the latest VMware technologies. For the full series, visit VMExplorer.
What can I run on BOM1? I have successfully deployed a simple VCF deployment, but I don’t recommend running VCF Automation on this BOM.
What VCF 9 products are running in BOM1? Initial components include: VCSA, VCF Operations, VCF Collector, NSX Manager, Fleet Manager, and SDDC Manager all running on the 3 x Nested ESX Hosts.
What are your plans for BOM2? Currently, under development but I would like to see if I could push the full VCF stack to it.
What can I run on BOM2? Under development, updates soon.
Are you running both BOMs configurations? No I’m only running one at a time. Currently, running BOM2.
Do I really need this much hardware? No you don’t. The parts listed on my BOM is just how I did it. I used some parts I had on hand and some I bought used. My recommendation is use what you have and upgrade when you need to.
What should I do to help with performance? Invest in highspeed disk, CPU cores, and RAM. I highly recommend lots of properly deployed NVMe disks for your nested ESX hosts. Make sure you adjust performance in Windows 11.
What do I need for multiple NVMe Drives? If you plan to use multiple NVMe drives into a single PCIe slot you’ll need a motherboard that supports bifurcation OR you’ll need an PCIe NVMe adapter that will support it. Not all NVMe adapters are the same, so do your research before buying.
VMware Workstation Gen 9: Part 7 Deploying VCF 9.0.1 Fleet
Now that I have set up an VCF 9 Offline depot and downloaded the installation media its time to deploy a Simple VCF 9 Fleet on my Workstation environment. With all my ESX host configured/powered on and the SDDC Installer ready here are the steps I took to complete this.
PRE-Steps
Optional:
1) One of the more important steps is making sure I backup my Workstation environment and delete any Workstation VM snapshots. This way my environment is ready for deployment.
2) Make sure your Windows 11 PC power plan is set to High Performance and does not put the computer to sleep.
3) Review the Planning and Resource Workbook.
Required:
4) Ensure the NTP Service is running on each of your hosts. TIP: Even if you setup the NTP to start and stop with host, you may have to go in to the host client and actually start the NTP service.
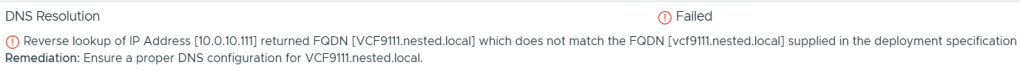
5) DNS can be a big issue for the VCF9 installer. I only setup the DNS names for the ESX Hosts and installers appliances. When I am going through the VCF Installer is when I setup the other DNS names. Example – NSX Manager, Automation, Operations appliances. I find this approach helps to minimize errors.
TIP: The VCF installer may show errors during the installation and validation processes. I ensure the ESX hostname case matches how it is registered in DNS. Example – Hostname vcf111.nested.local doesn’t equal VCF111.nested.local.
6) With my ESX Hostnames confirmed in DNS, I need to update their self-signed certificates. See the following URL’s.
- KB: VCF Installer fails to add hosts during deployment due to hostname mismatch with subject alternative name
- DOCS: Regenerate the Self-Signed Certificate on ESX Hosts
- NOTE: Make sure you reboot your host via the DCUI and not via command line. I noted that after I regenerated the self-signed certificate I rebooted the host via command line. This caused the regenerated certificate to not take. If I rebooted the host via the DCUI the new certificate would take.
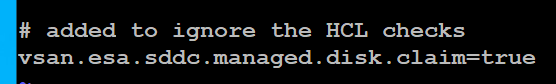
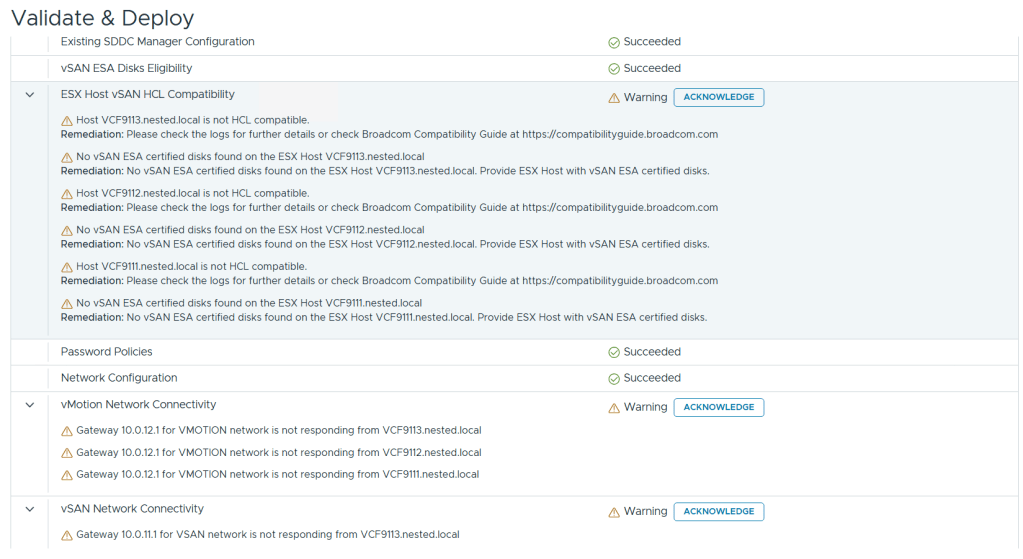
7) The VCF Installer 9.0.1 has some extra features to allow non-vSAN certified disks to pass the validation section. However, nested hosts will fail the HCL checks. Simply add the line below to the /etc/vmware/vcf/domainmanager/application-prod.properties and then restart the SDDC Domain Manager services with the command: systemctl restart domainmanager
This allows me Acknowledge the errors and move the deployment forward.
Installing VCF 9 with the VCF Installer
I log into the VCF Installer.
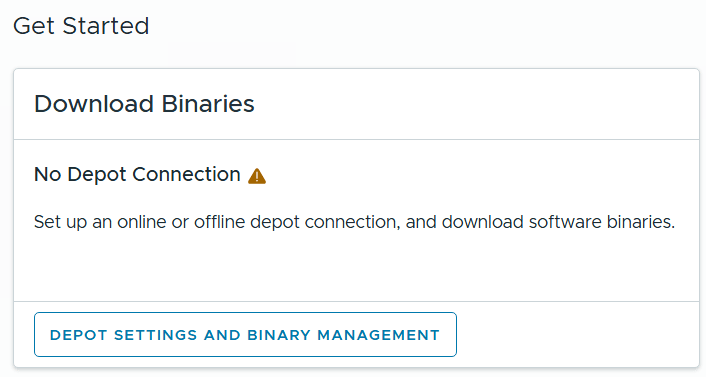
I click on ‘Depot Settings and Binary Management’
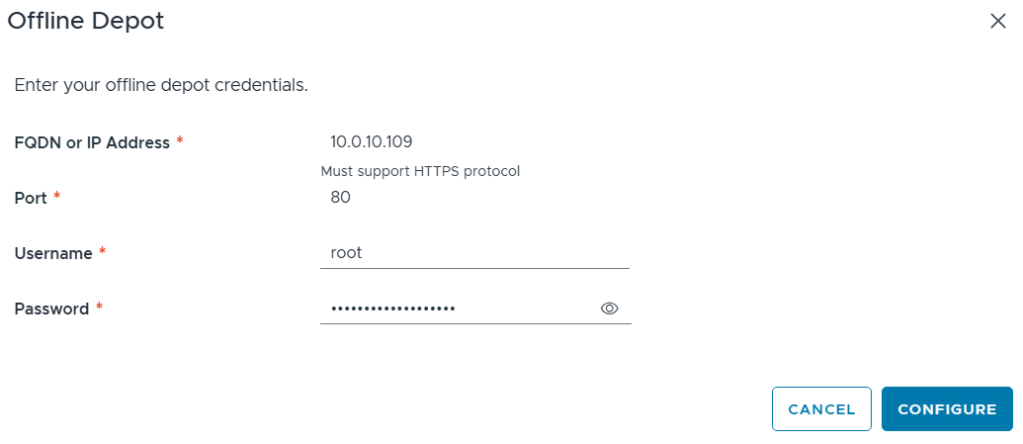
I click on ‘Configure’ under Offline Depot and then click Configure.
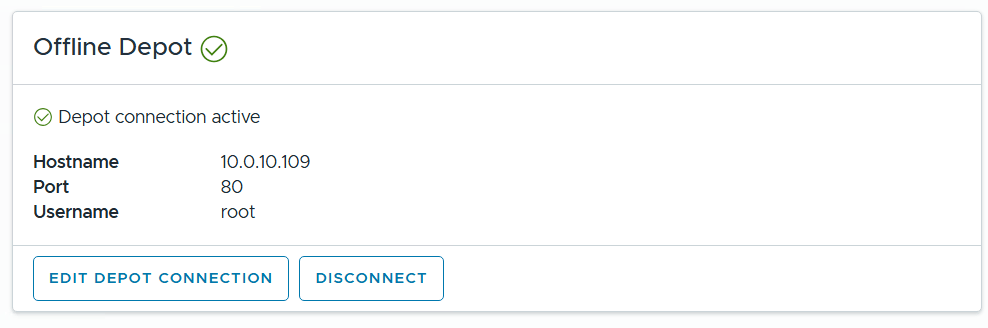
I confirm the Offline Depot Connection if active.
I chose ‘9.0.1.0’ next to version, select all except for VMware Cloud Automation, then click on Download.

Allow the downloads to complete.
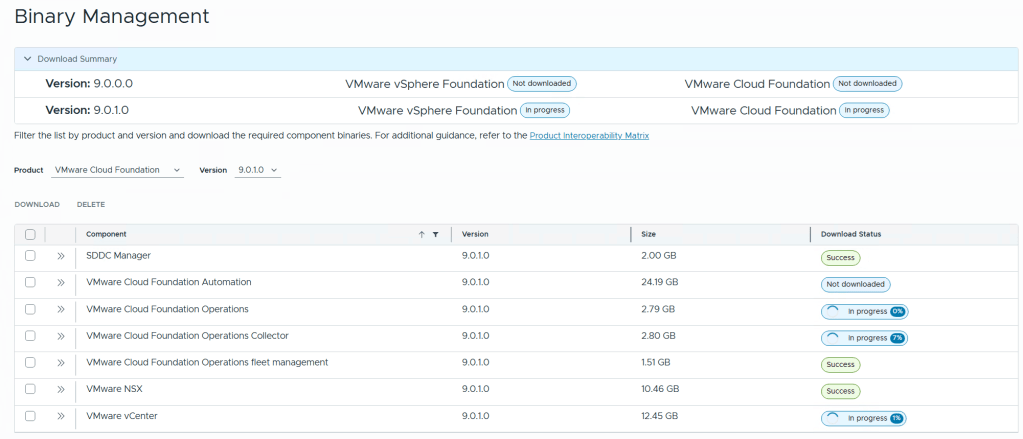
All selected components should state “Success” and the Download Summary for VCF should state “Partially Downloaded” when they are finished.

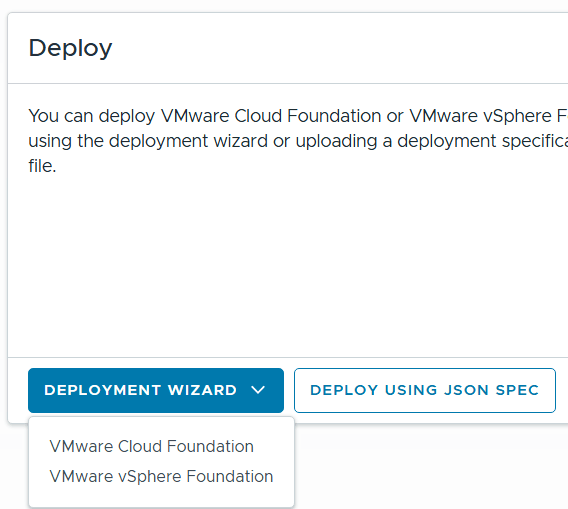
Click return home and choose VCF under Deployment Wizard.
This is my first deployment so I’ll choose ‘Deploy a new VCF Fleet’
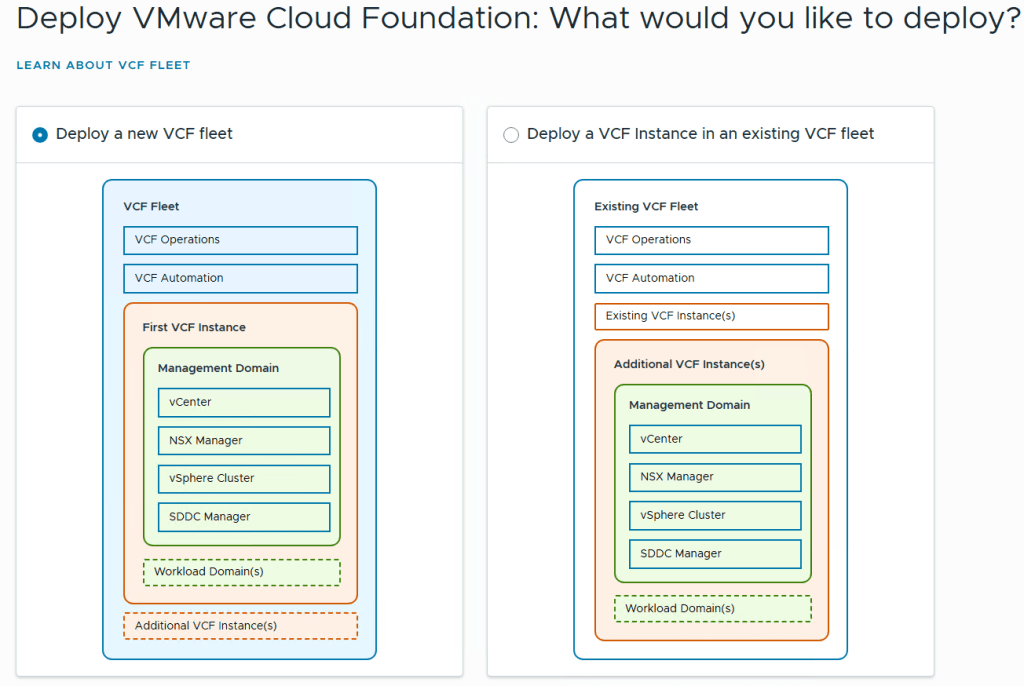
The Deploy VCF Fleet Wizard starts and I’ll input all the information for my deployment.
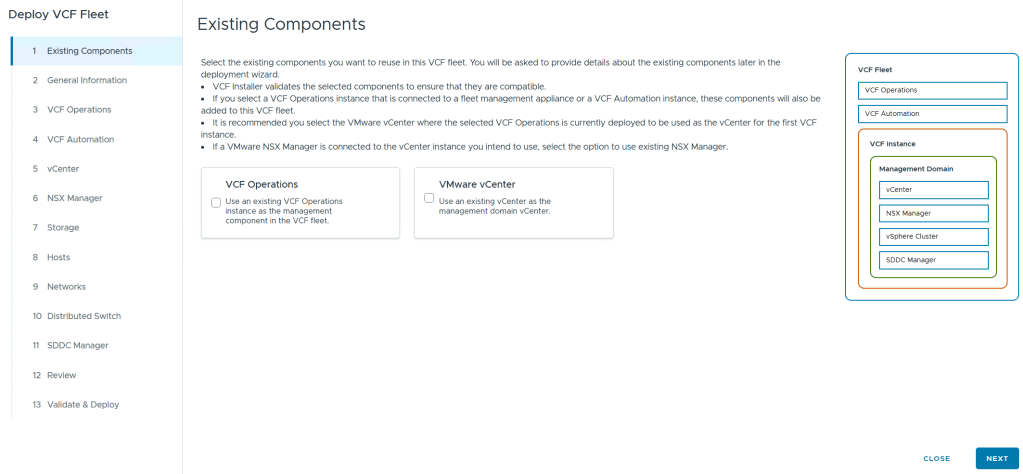
For Existing Components I simply choose next as I don’t have any.
I filled in the following information around my environment, choose simple deployment and clicked on next.

I filled out the VCF Operations information and created their DNS records. Once complete I clicked on next.

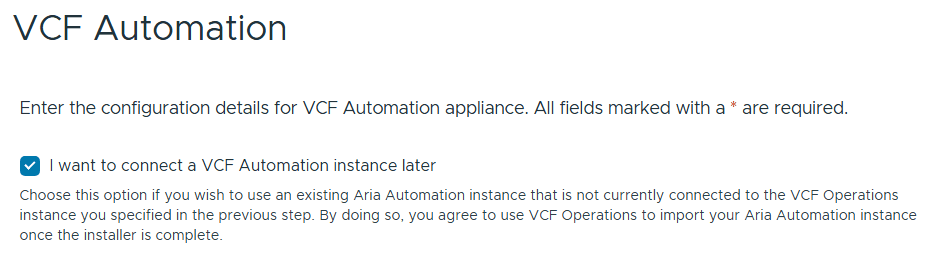
I chose to “I want to connect a VCF Automation instance later” can chose next.
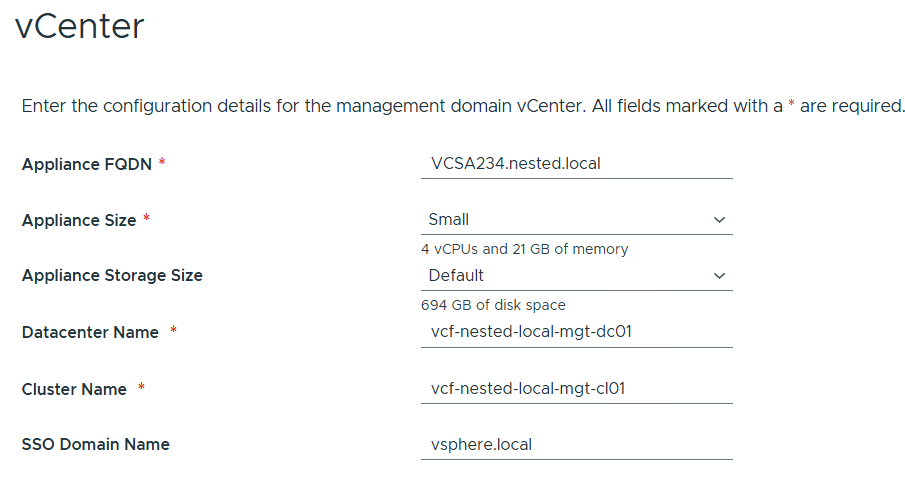
Filled out the information for vCenter
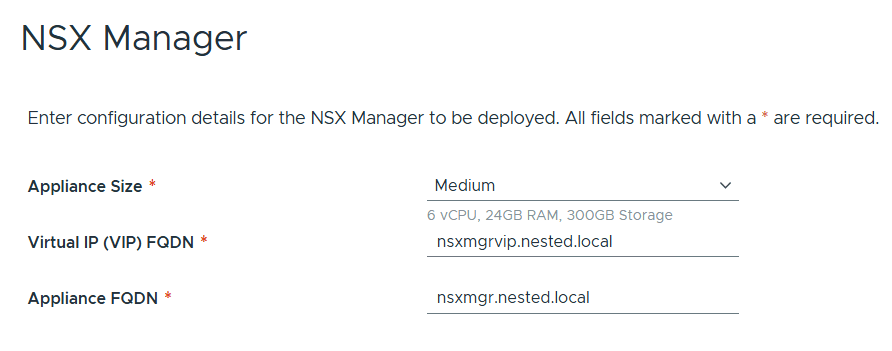
Entered the details for NSX Manager.
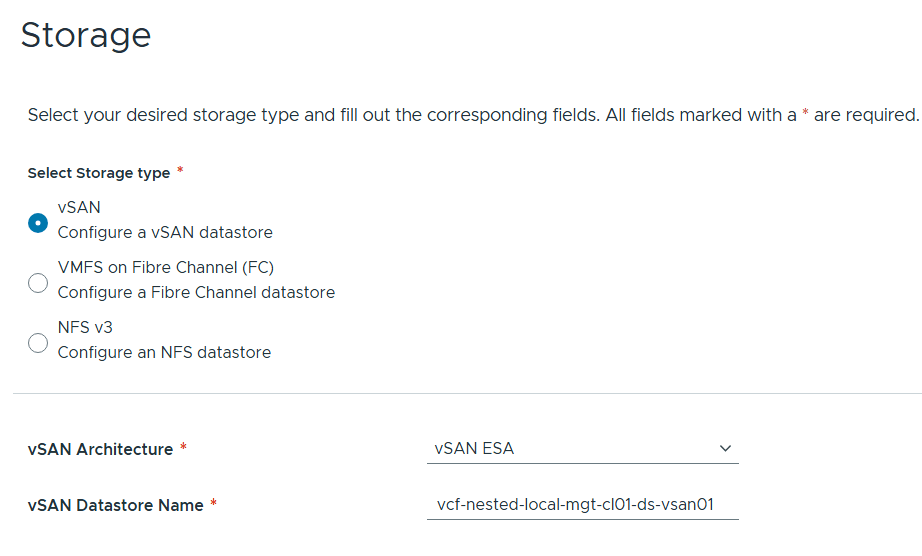
Left the storage items as default.
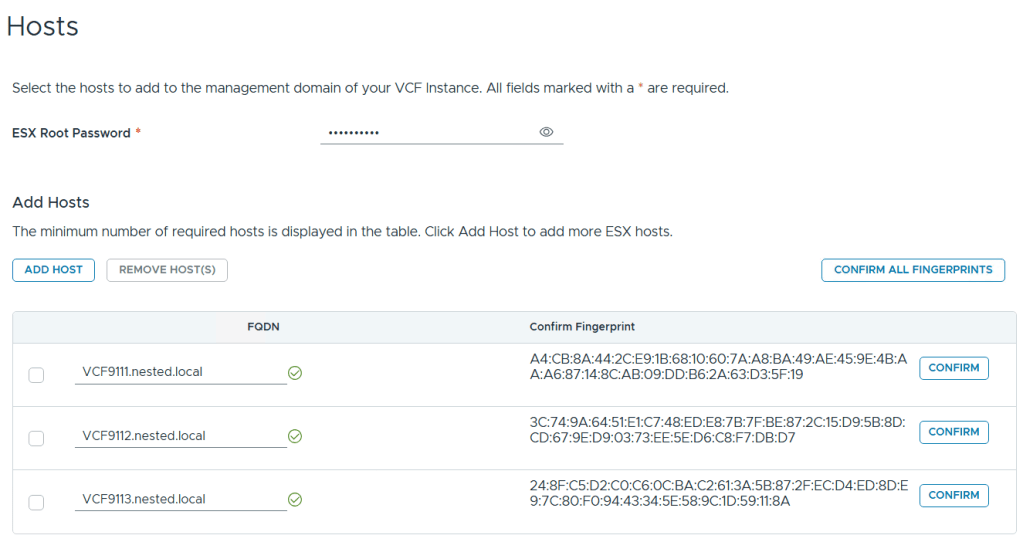
Added in my 3 x ESX 9 Hosts, confirmed all fingerprints, and clicked on next.
Note: if you skipped the Pre-requisite for the self-signed host certificates, you may want to go back and update it before proceeding with this step.
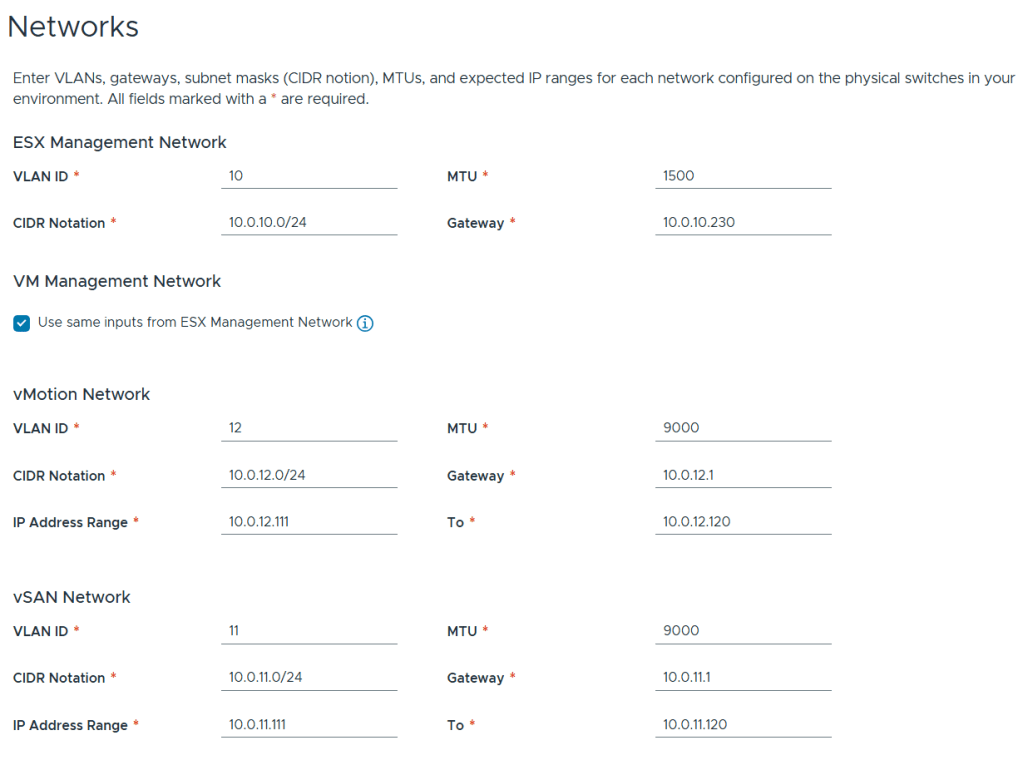
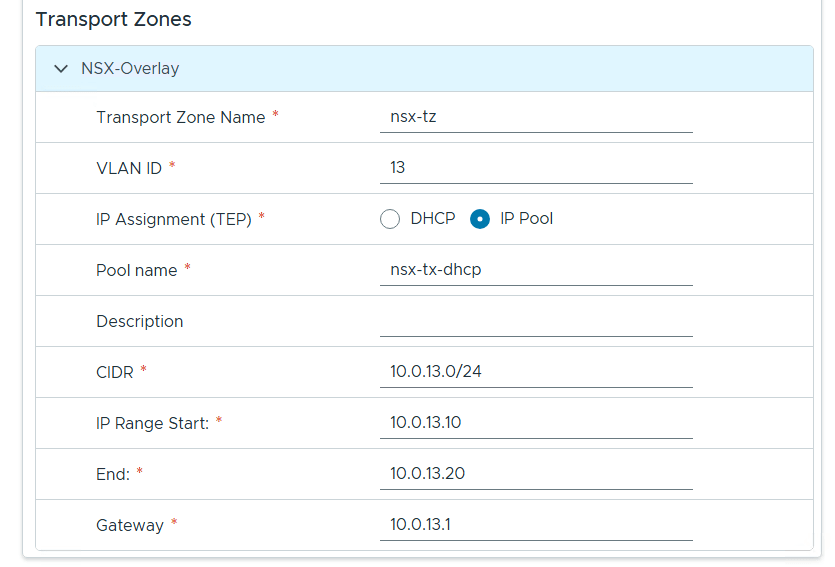
Filled out the network information based on our VLAN plan.
For Distributed Switch click on ‘Select’ under ‘Custom Switch Configuration’
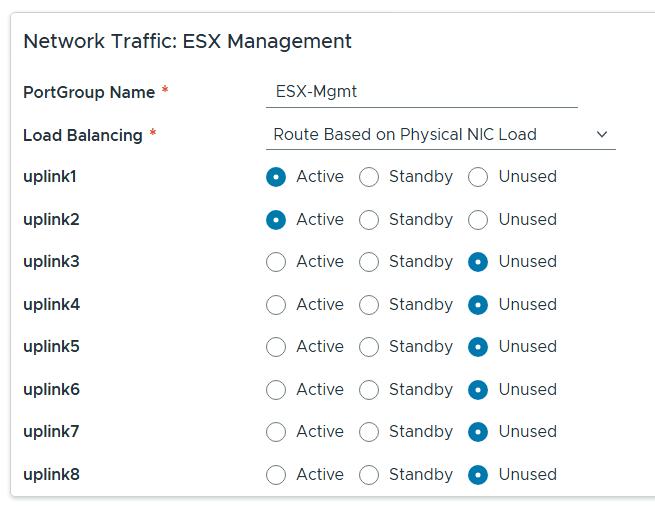
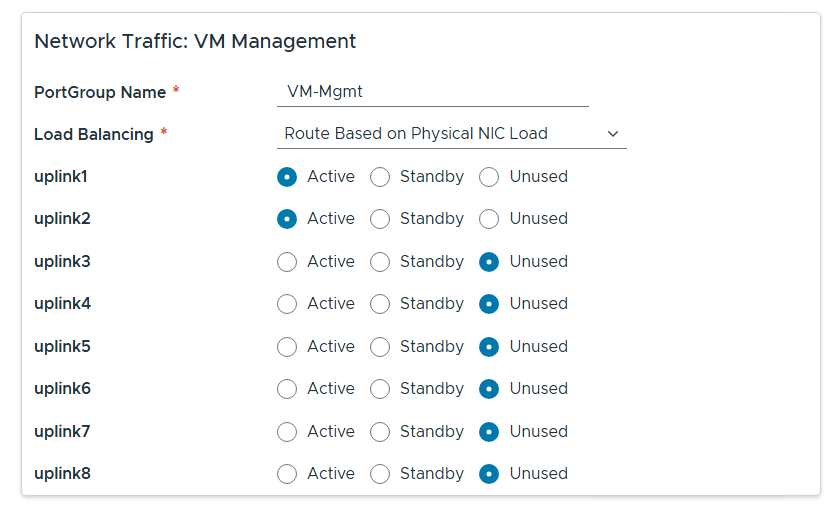
Click on the vDS Switch name. Put in MTU 9000, change uplinks to 8 and chose all switches for ‘Configure network traffic(s) for this Distributed Switch, then scroll down.

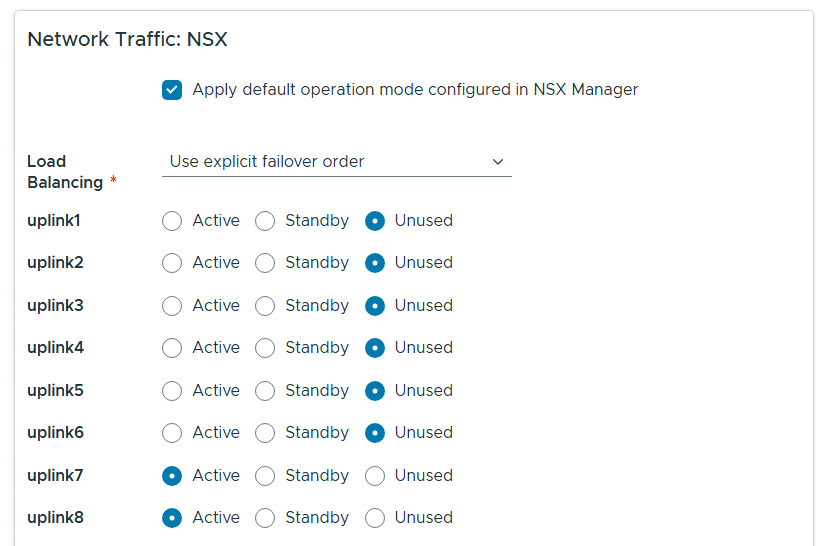
Rename each port group, set load balancing to ‘Route based on Physical NIC load’, select the correct uplinks as active, select the correct uplinks ad unused.


Configure NSX as follows.
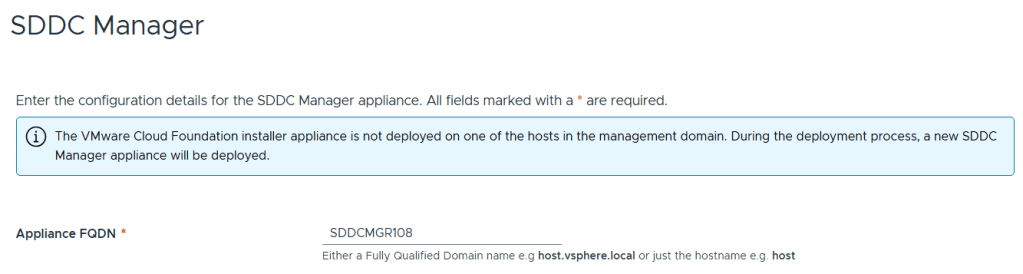
Entered the name of the new SDDC Manager and updated it’s name in DNS, then clicked on next.
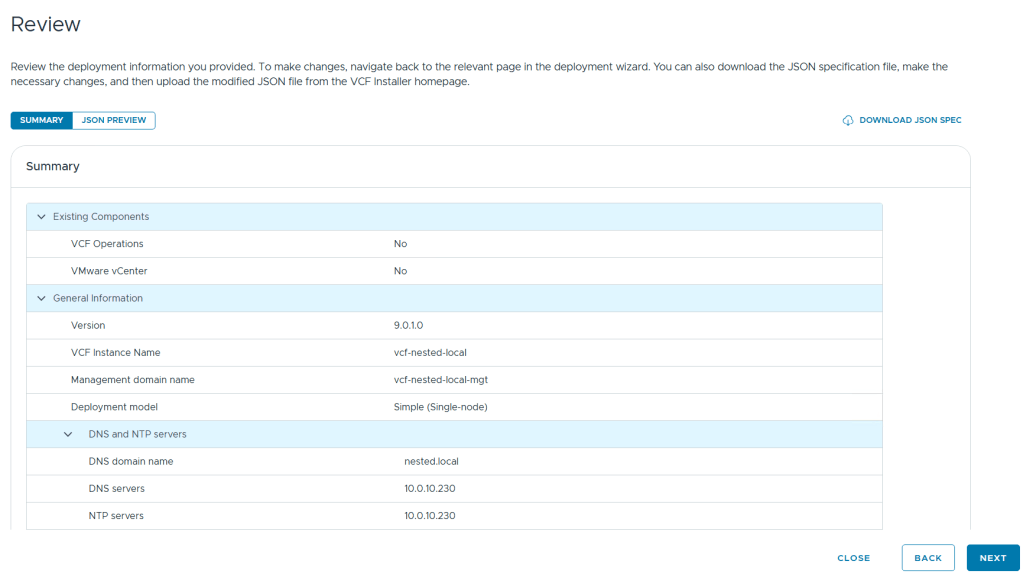
Reviewed the deployment information and chose next.
TIP – Download this information as a JSON Spec, can save you a lot of typing if you have to deploy again.
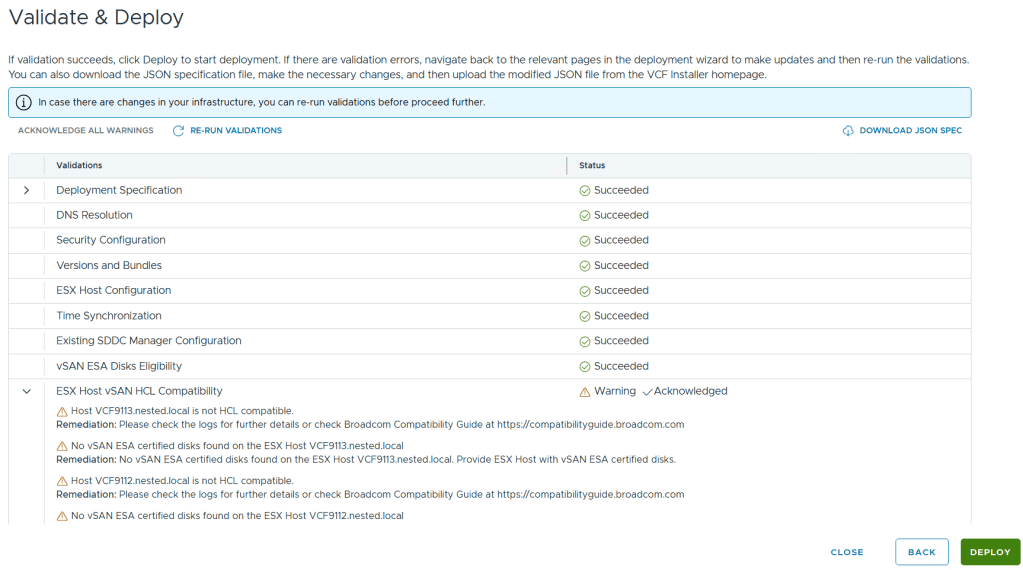
Allow it to validate the deployment information.
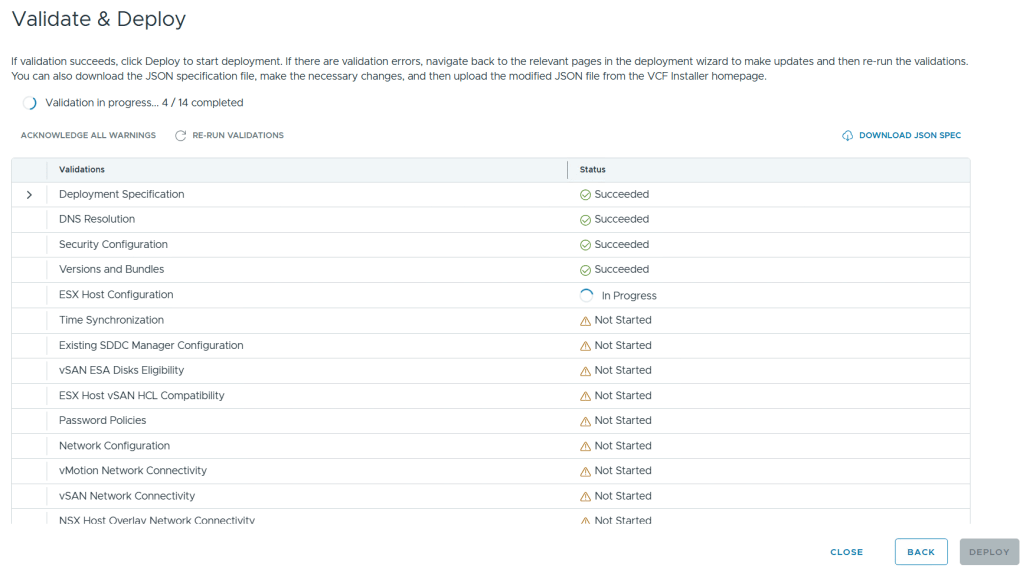
I reviewed the validation warnings, at the top click on “Acknowledge all Warnings” and click ‘DEPLOY’ to move to the next step.
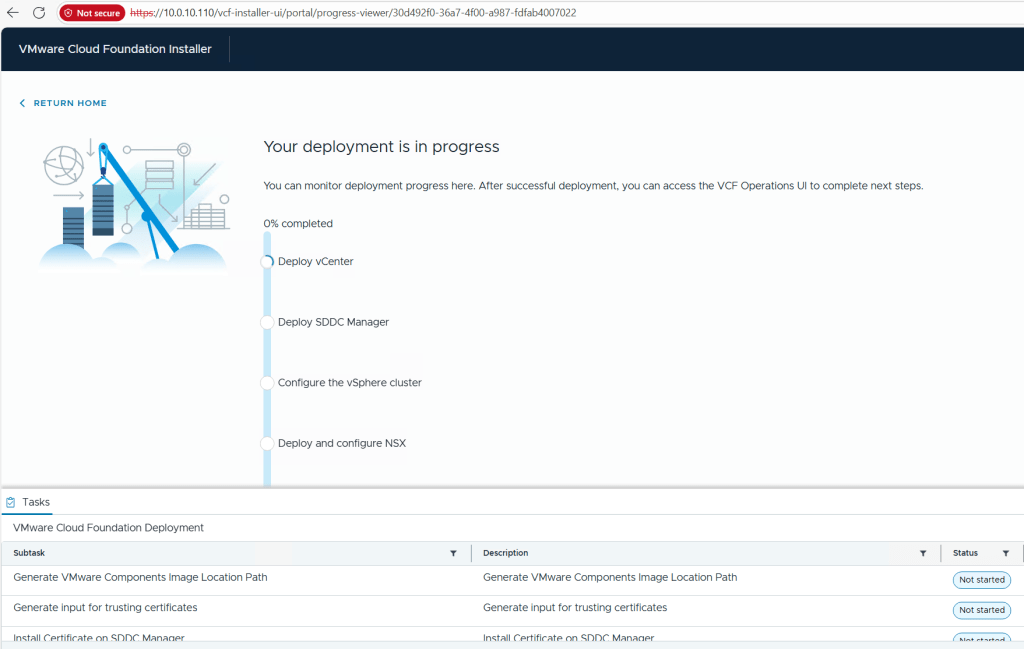
Allow the deployment to complete.
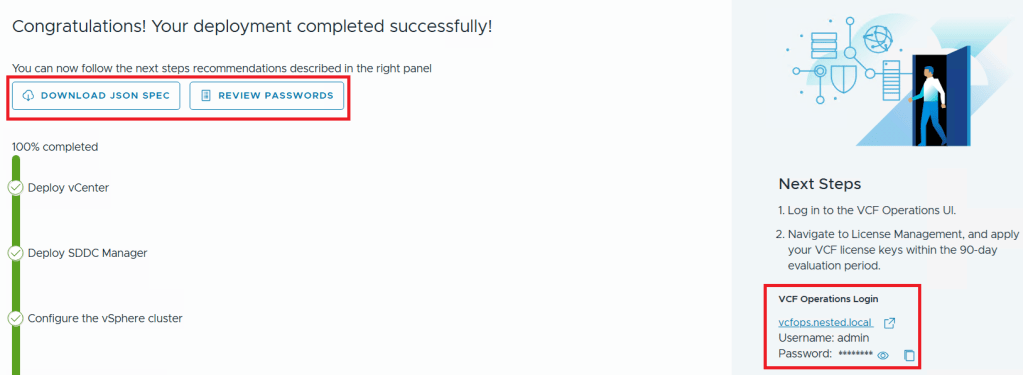
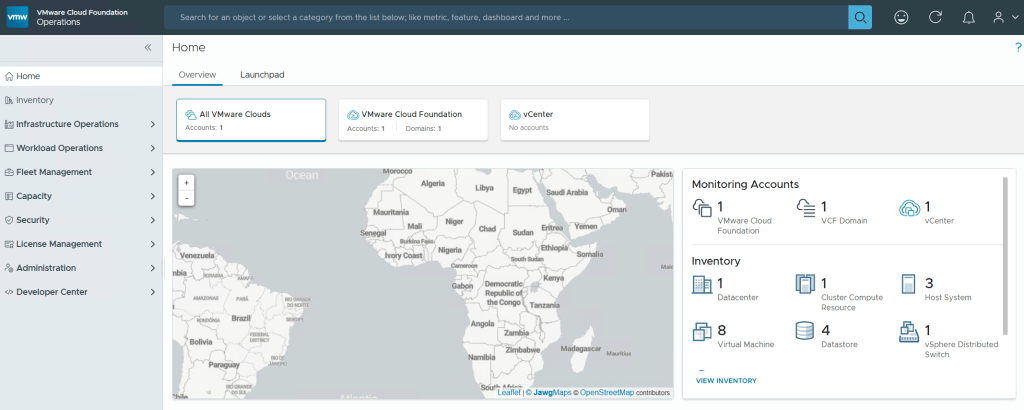
Once completed, I download the JSON SPEC, Review and document the passwords, (Fig-1) and then log into VCF Operations. (Fig-2)
(Fig-1)
(Fig-2)
Now that I have a VCF 9.0.1 deployment complete I can move on to Day N tasks. Thanks for reading and reach out if you have any questions.
VMware Workstation Gen 9: Part 6 VCF Offline Depot
To deploy VCF 9 the VCF Installer needs access to the VCF installation media or binaries. This is done by enabling Depot Options in the VCF Installer. For users to move to the next part, they will need to complete this step using resources available to them. In this blog article I’m going to supply some resources to help users perform these functions.
Why only supply resources? When it comes to downloading and accessing VCF 9 installation media, as a Broadcom/VMware employee, we are not granted the same access as users. I have an internal process to access the installation media. These processes are not publicly available nor would they be helpful to users. This is why I’m supplying information and resources to help users through this step.
What are the Depot choices in the VCF Installer?
Users have 2 options. 1) Connect to an online depot or 2) Off Line Depot
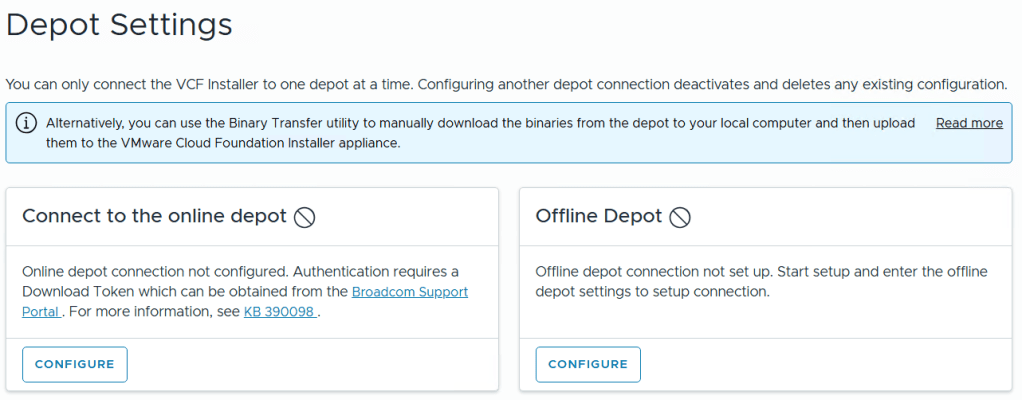
What are the requirements for the 2 Depot options?
1) Connect to an online depot — Users need to have an entitled support.broadcom.com account and a download token. Once their token is authenticated they are enabled to download.
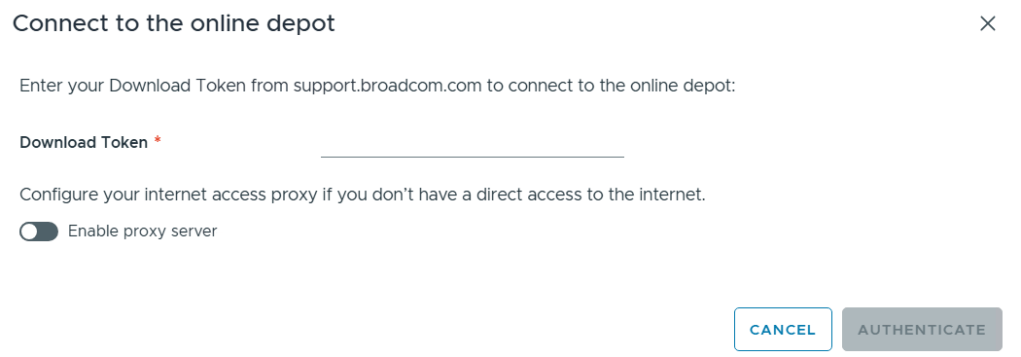
See These URL’s for more information:
2) Offline Depot -The VCF 9 Offline Depot Tool (also known as the VCF Download Tool or VCFDT) is a specialized utility designed for VMware Cloud Foundation 9.0 to enable the deployment, patching, and upgrading of private cloud environments in air-gapped (disconnected) or restricted environments. It acts as an internal mirror of the official Broadcom online depot, allowing administrators to host necessary software binaries and metadata locally.
This option may be more common for users building out Home labs.
I’ll be using the Offline Depot method to download my binaries and in the next part I’ll be deploying VCF 9.0.1.
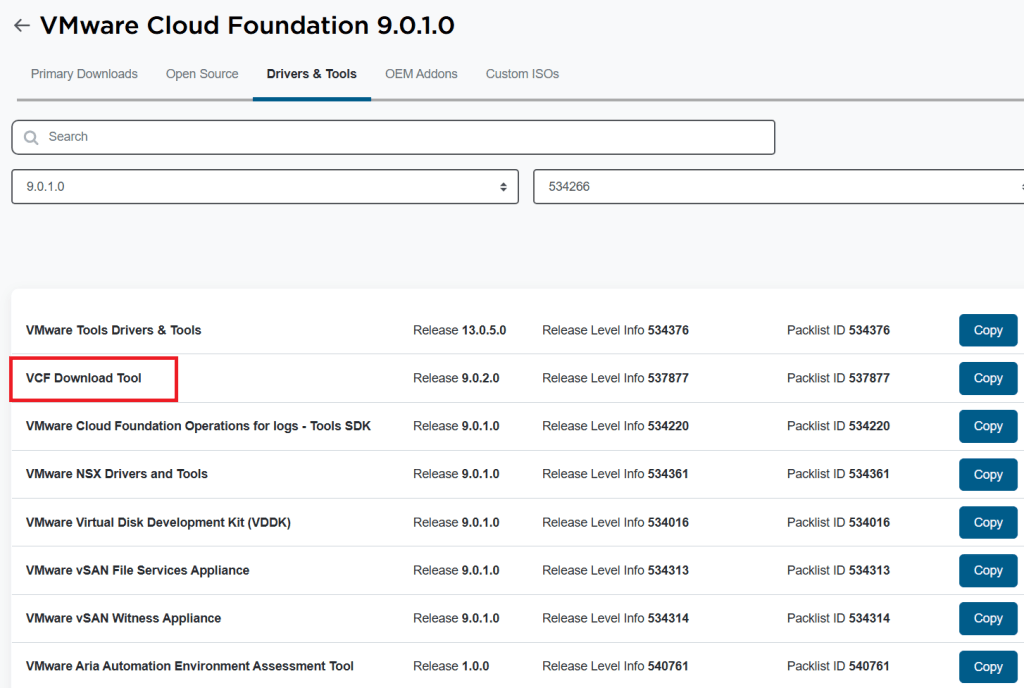
Where is the Offline Depot tool located?
Go to support.broadcom.com > My Downloads > VMware > Search for Cloud Foundation. Find your version of Cloud foundation and then click on ‘Drivers and Tools’
See these URLs for more information:
- Set Up an Offline Depot Web Server for VMware Cloud Foundation
- Set Up an Offline Depot Web Server for VMware Cloud Foundation << Use this method if you want to setup https on the Photon OS.
- How to deploy VVF/VCF 9.0 using VMUG Advantage & VCP-VCF Certification Entitlement
- Setting up a VCF 9.0 Offline Depot
VMware Workstation Gen 9: Part 5 Deploying the VCF Installer with VLANs
The VCF Installer (aka SDDC Manager Appliance) is the appliance that will allow me to deploy VCF on to my newly created ESX hosts. The VCF Installer can be deployed on to a ESX Host or directly on Workstation. There are a couple of challenges with this deployment in my Home lab and in this blog post I’ll cover how I overcame this. It should be noted, the modifications below are strictly for my home lab use.
Challenge 1: VLAN Support
By default the VCF Installer doesn’t support VLANS. It’s a funny quandary as VCF 9 requires VLANS. Most production environments will allow you to deploy the VCF Installer and be able to route to a vSphere environment. However, my Workstation Home Lab uses LAN Segments which are local to Workstation. To communicate over LAN Segments all VMs must have a VLAN ID. To overcome this issue I’ll need to add VLAN support to the VCF Installer.
Challenge 2: Size Requirements
The installer takes up a massive 400+ GB of disk space, 16GB of RAM, and 4 vCPUs. The current configuration of my ESX hosts don’t have a datastore large enough to deploy it to, plus vSAN is not set up. To overcome this issue I’ll need to deploy it as a Workstation VM and attach it to the correct LAN Segment.
In the steps below I’ll show you how I added a VLAN to the VCF Installer, deployed it directly on Workstation, and ensure it’s communicating with my ESX Hosts.
Deploy the VCF Installer
Download the VCF Installer OVA and place the file in a location where Workstation can access it.
In Workstation click on File > Open. Choose the location of your OVA file and click open.
Check the Accept box > Next

Choose your location for the VCF Installer Appliance to be deployed. Additionally, you can change the name of the VM. Then click Next.
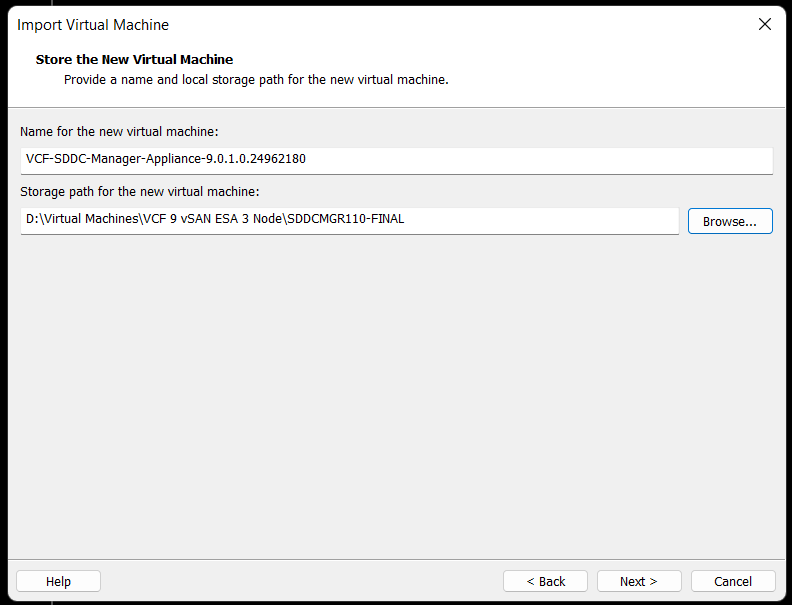
Fill in the passwords, hostname, and NTP Server. Do not click on Import at this time. Click on ‘Network Configuration’.
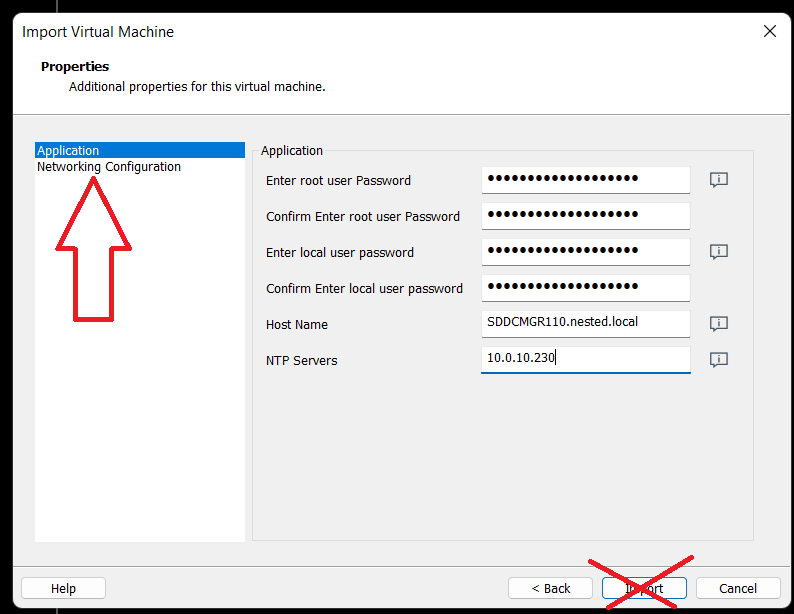
Enter the network configuration and click on import.

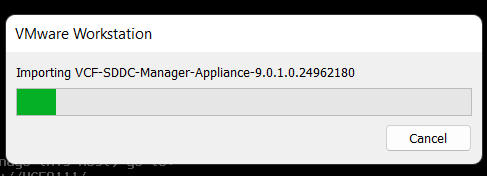
Allow the import to complete.
Allow the VM to boot.

Change the VCF Installer Network Adapter Settings to match the correct LAN Segment. In this case I choose 10 VLAN Management.

Enable VLAN support in the VCF Installer
1) Login as root and create the following file.
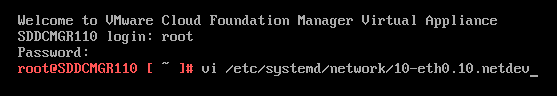
vi /etc/systemd/network/10-eth0.10.netdev
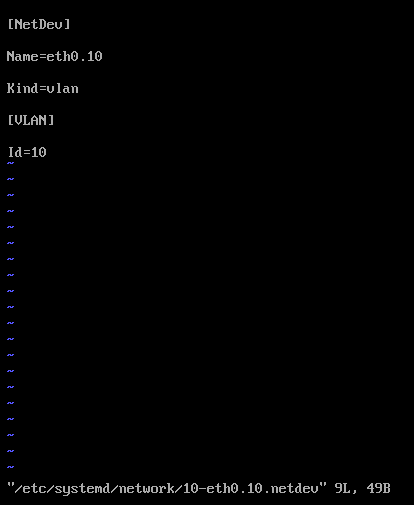
Press Insert the add the following
[NetDev]
Name=eth0.10
Kind=vlan
[VLAN]
Id=10
Press Escape, Press :, Enter wq! and press enter to save
2) Create the following file.
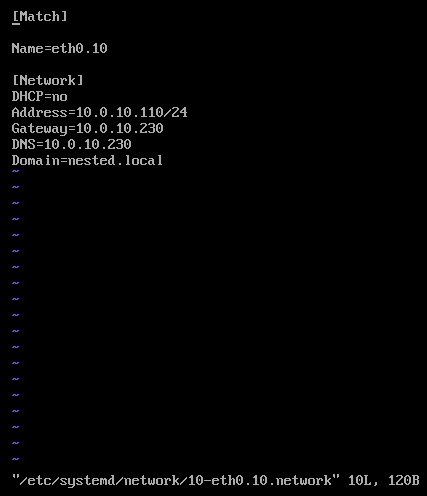
vi /etc/systemd/network/10-eth0.10.network
Press insert and add the following
[Match]
Name=eth0.10
[Network]
DHCP=no
Address=10.0.10.110/24
Gateway=10.0.10.230
DNS=10.0.10.230
Domain=nested.local
Press Escape, Press :, Enter wq! and press enter to save
3) Modify the original network file
vi /etc/systemd/network/10-eth0.network
Press Escape, Press Insert, and remove the static IP address configuration and change the configuration as following:
[Match]
Name=eth0
[Network]
VLAN=eth0.10
Press Escape, Press :, Enter wq! and press enter to save

4) Update the permissions to the newly created files
chmod 644 /etc/systemd/network/10-eth0.10.netdev
chmod 644 /etc/systemd/network/10-eth0.10.network
chmod 644 /etc/systemd/network/10-eth0.network
5) Restart services or restart the vm.
systemctl restart systemd-networkd
6) Check the network status of the newly created network eth0.10
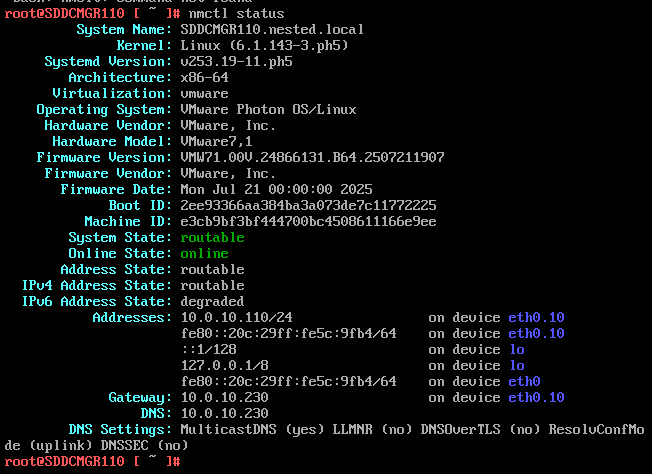
nmctl status
7) Do a ping test from the VCF Installer appliance.
Note – The firewall needs to be adjusted to allow other devices to ping the VCF Installer appliance.
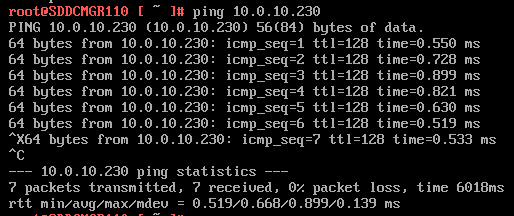
Ping 10.0.10.230
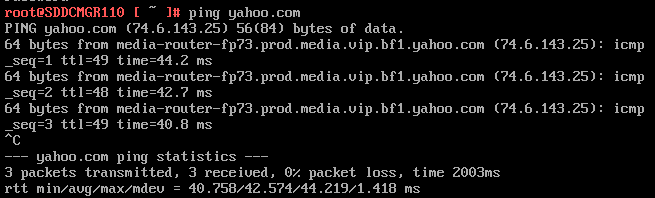
Next I do ping to an internet location to confirm this appliance can route to the internet.
8) Allow SSH access to the VCF Installer Appliance
Follow this BLOG to allow SSH Access.
From the Windows AD server or other device on the same network, putty into the VCF Installer Appliance.

Adjust the VCF Installer Firewall to allow inbound traffic to the new adapter
Note – Might be a good time to make a snapshot of this VM.
1) From SSH check the firewall rules for the VCF Installer with the following command.
iptables -L –verbose –line-numbers
From this output I can see that eth0 is set up to allow access to https, ping, and other services. However, there are no rules for the eth0.10 adapter. I’ll need to adjust the firewall to allow this traffic.

Next I insert a new rule allowing all traffic to flow through e0.10 and check the rule list.
iptables -I INPUT 4 -i eth0.10 -j ACCEPT
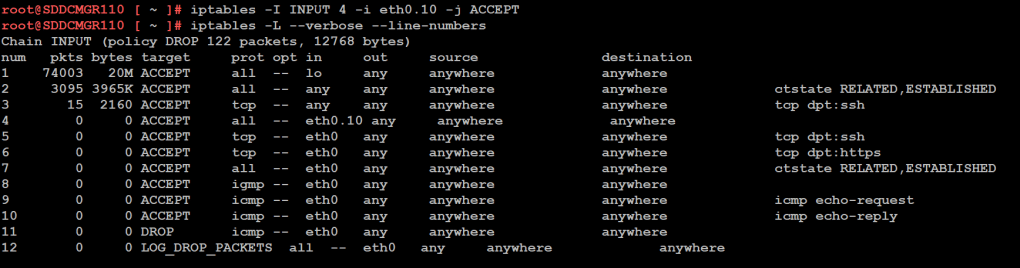
The firewall rules are not static. To make the current firewall rules stay static I need to save the rules.
Save Config Commands
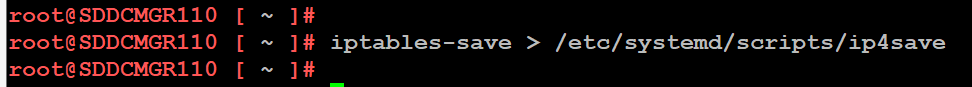
Restart and make sure you can now access the VCF Installer webpage, and I do a ping test again just to be sure.
Now that I got VCF Installer installed and working on VLANs I’m now ready to deploy the VCF Offline Depot tool into my environment and in my next blog post I’ll do just that.
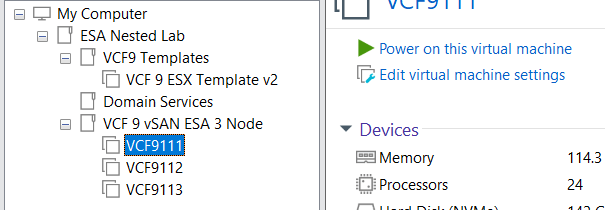
VMware Workstation Gen 9 Part 4 ESX Host Deployment and initial configuration
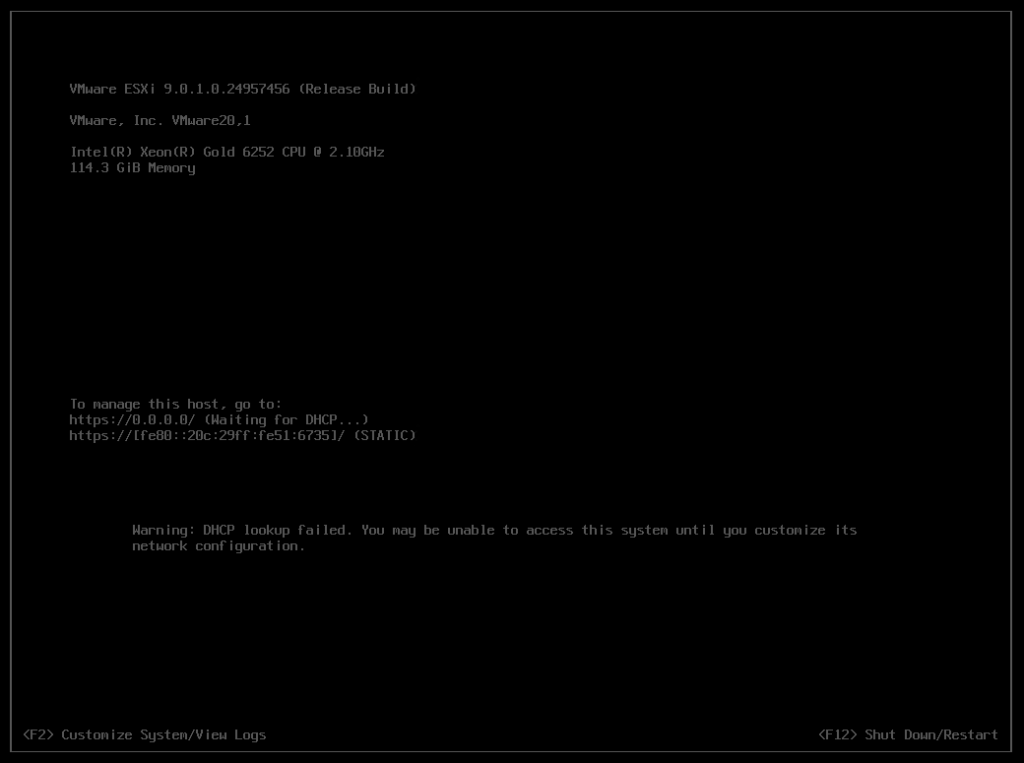
Now that I created 3 ESX hosts from templates it is time to install ESX. To do this I simply power on the Hosts and follow the prompts. The only requirement at this point is my Windows Server and Core Services be up and functional. In this blog we’ll complete the installation of ESX.
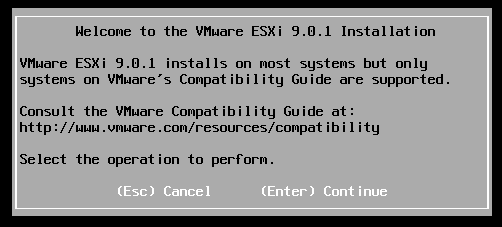
Choose a host then click on “Power on this virtual machine”.
The host should boot to the ESX ISO I choose when I created my template.
Choose Enter to Continue
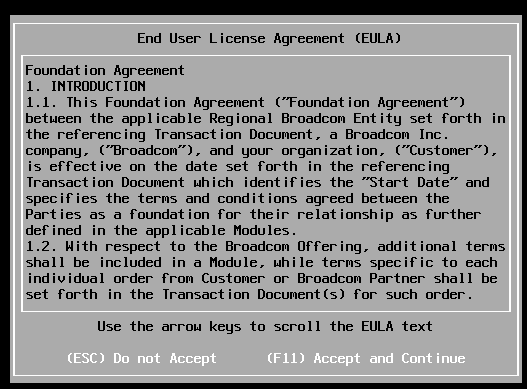
Choose F11 to Accept and Continue
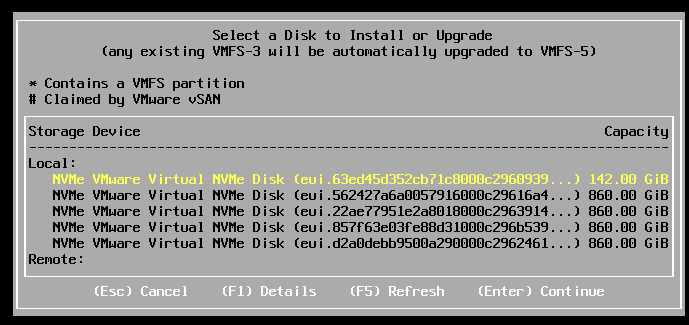
If the correct boot disk is selected, press Enter to continue.
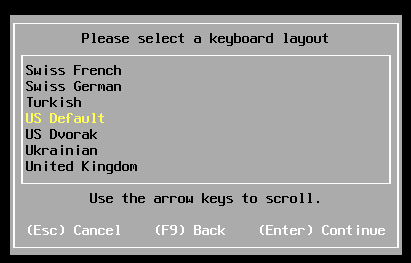
Choose pressed enter to accept the US Default keyboard layout
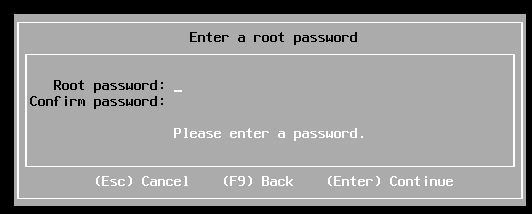
Entered a root password and pressed enter.
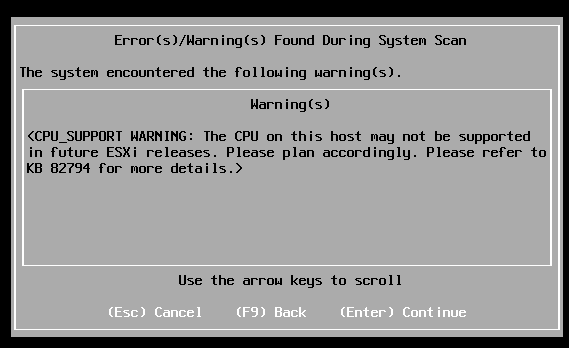
Pressed enter at the warning of CPU support.
Pushed F11 to install
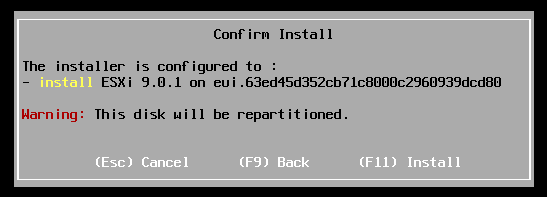
Allowed ESX to install.

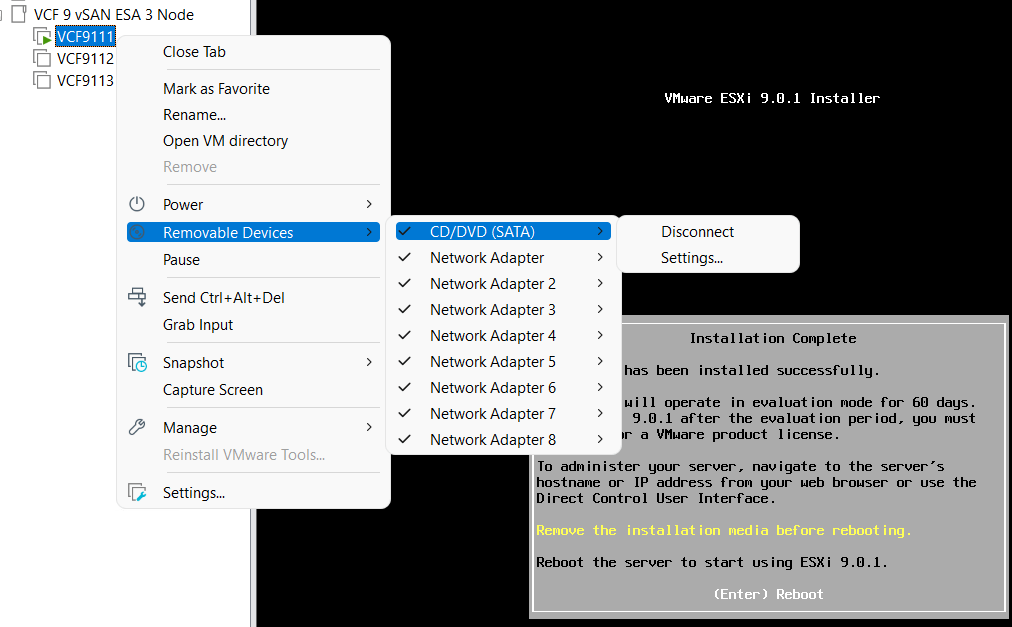
Disconnected the media and pressed enter to reboot
Once rebooted I choose F2 to customize the system and logged in with my root password
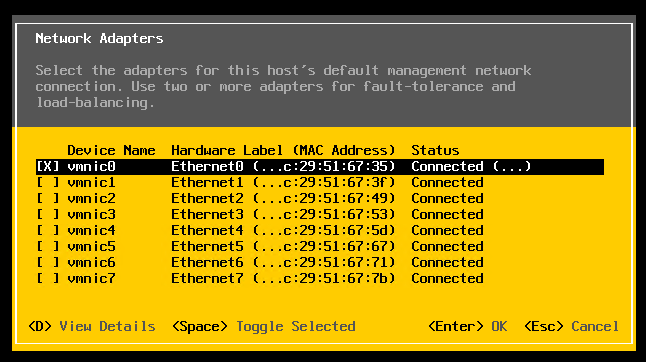
Choose Configure Management Network > Network Adapters, and validate the vmnic0 is selected, then pressed escape
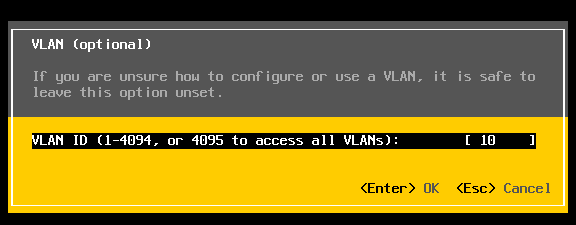
Choose VLAN (optional) > Entered in 10 for my VLAN > pressed enter to exit
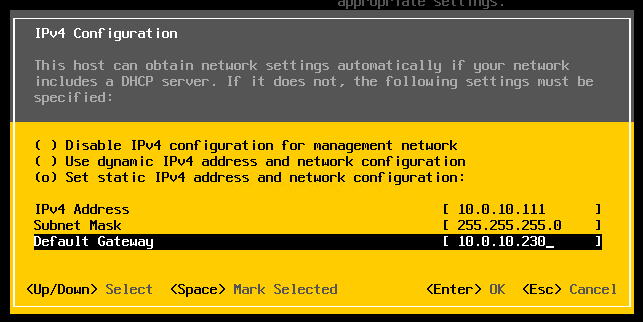
Choose IPv4 Configuration and enter the following for VCF9111 host and then pressed enter.
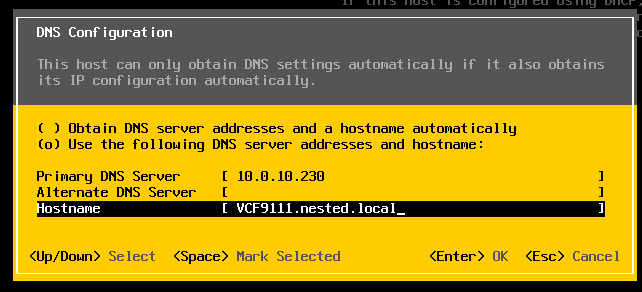
Choose DNS Configuration and enter the following.
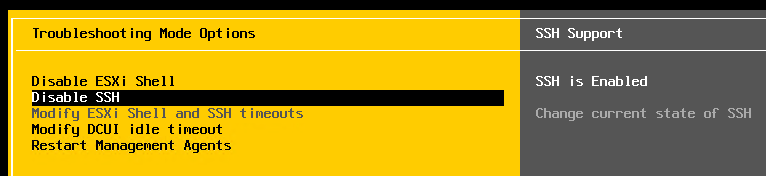
Press Escape to go to the main screen. Press Y to restart management. Arrow down to ‘Enable ESXi Shell” and press enter, then the same for SSH. Both should now be enabled.
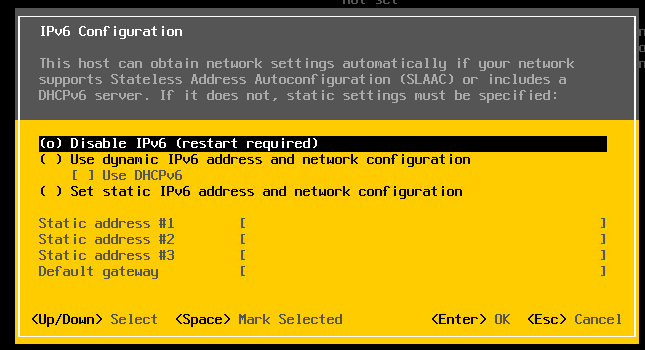
Press Escape and choose Configure Management Network. Next choose IPv6 Configuration, choose “Disable IPv6” and press enter.
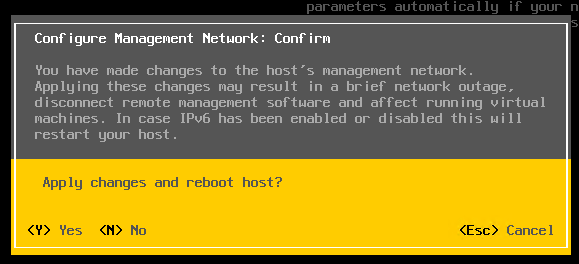
Press Escape and the host will prompt you to reboot, press Y to reboot.
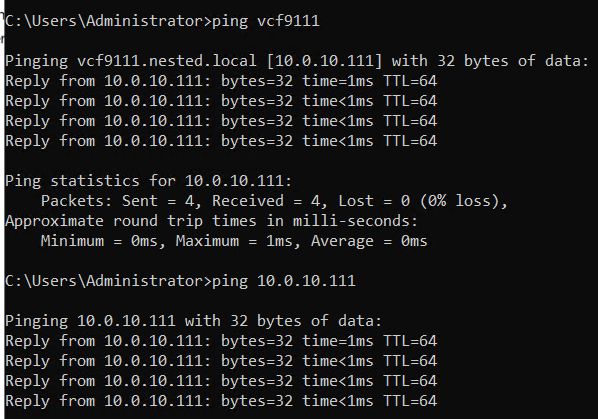
Test connectivity
From the AD server simply ping the VCF9111 host. This test ensures DNS is working properly and the LAN Segment is passing VLAN10.
From here I repeat this process for the other 2 hosts, only assigning them unique IPs.
Next up Deploying the VCF Installer with VLANs.
