programming
Using PowerShell to setup AV exceptions for Workstation 25H2u1 and Windows 11
Adding AV exceptions to your Workstation deployment on Windows 11 can really improve the overall performance. In this blog post I’ll share my exclusion script recently used on my environment.
NOTE: You cannot just cut, paste, and run the script below. There are parts of the script that have to be configured for the intended system.
What the script does.
- For Windows 11 users with Microsoft’s Virus & threat protection enabled this script will tell AV to not scan specific file types, folders, and processes related to VMware Workstation.
- It will ignore exceptions that already exist.
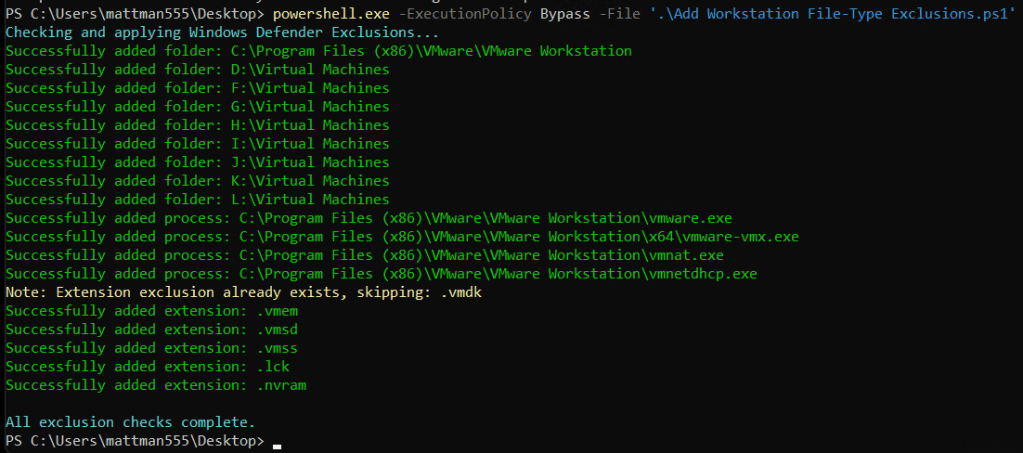
- It will display appropriate messages (Successful, or Already Exists) as it completes tasks.
What is the risk?
- Adding an exception (or exclusion) to antivirus (AV) software, while sometimes necessary for application functionality, significantly lowers the security posture of a device. The primary risk is creating a security blind spot where malicious code can be downloaded, stored, and executed without being detected.
- Use at your own risk. This code is for my personal use.
What will the code do?
It will add several exclusions listed below.
- File Type: Exclude these specific VMware file types from being scanned:
- .vmdk: Virtual machine disk files (the largest and most I/O intensive).
- .vmem: Virtual machine paging/memory files.
- .vmsn: Virtual machine snapshot files.
- .vmsd: Metadata for snapshots.
- .vmss: Suspended state files.
- .lck: Disk consistency lock files.
- .nvram: Virtual BIOS/firmware settings.
- Folder: Unique to my deployment it will exclude the following directories to prevent your antivirus from interfering with VM operations
- VMware Installation folder
- VM Storage Folders: Exclude the main directory where I store my virtual machines.
- Installation Folder: Exclude the VMware Workstation installation path ((default: C:\Program Files (x86)\VMware\VMware Workstation).
- Process:
- vmware.exe: The main Workstation interface.
- vmware-vmx.exe: The core process that actually runs each virtual machine.
- vmnat.exe: Handles virtual networking (NAT).
- vmnetdhcp.exe: Handles DHCP for virtual networks.
The Script
Under the section ‘#1. Define your exclusions ‘ is where I adapted this code to match my environment
# Check for Administrator privileges
if (-not ([Security.Principal.WindowsPrincipal][Security.Principal.WindowsIdentity]::GetCurrent()).IsInRole([Security.Principal.WindowsBuiltInRole]::Administrator)) {
Write-Warning "Please run this script as an Administrator."
break
}
# 1. Define your exclusions
# This is where you put in YOUR folder exclusions
$folders = @("C:\Program Files (x86)\VMware\VMware Workstation", "D:\Virtual Machines", "F:\Virtual Machines", "G:\Virtual Machines", "H:\Virtual Machines", "I:\Virtual Machines", "J:\Virtual Machines", "K:\Virtual Machines", "L:\Virtual Machines")
# These are the common process exclusions
$processes = @("C:\Program Files (x86)\VMware\VMware Workstation\vmware.exe", "C:\Program Files (x86)\VMware\VMware Workstation\x64\vmware-vmx.exe", "C:\Program Files (x86)\VMware\VMware Workstation\vmnat.exe", "C:\Program Files (x86)\VMware\VMware Workstation\vmnetdhcp.exe")
# These are the common extension exclusions
$extensions = @(".vmdk", ".vmem", ".vmsd", ".vmss", ".lck", ".nvram")
# Retrieve current settings once for efficiency
$currentPrefs = Get-MpPreference
Write-Host "Checking and applying Windows Defender Exclusions..." -ForegroundColor Cyan
# --- Validate and Add Folders ---
foreach ($folder in $folders) {
if ($currentPrefs.ExclusionPath -contains $folder) {
Write-Host "Note: Folder exclusion already exists, skipping: $folder" -ForegroundColor Yellow
} else {
Add-MpPreference -ExclusionPath $folder
Write-Host "Successfully added folder: $folder" -ForegroundColor Green
}
}
# --- Validate and Add Processes ---
foreach ($proc in $processes) {
if ($currentPrefs.ExclusionProcess -contains $proc) {
Write-Host "Note: Process exclusion already exists, skipping: $proc" -ForegroundColor Yellow
} else {
Add-MpPreference -ExclusionProcess $proc
Write-Host "Successfully added process: $proc" -ForegroundColor Green
}
}
# --- Validate and Add Extensions ---
foreach ($ext in $extensions) {
if ($currentPrefs.ExclusionExtension -contains $ext) {
Write-Host "Note: Extension exclusion already exists, skipping: $ext" -ForegroundColor Yellow
} else {
Add-MpPreference -ExclusionExtension $ext
Write-Host "Successfully added extension: $ext" -ForegroundColor Green
}
}
Write-Host "`nAll exclusion checks complete." -ForegroundColor Cyan
The Output
In the output below, when the script creates an item successfully it will show in green. If it detects a duplicate it will output a message in yellow. I ran the script with a .vmdk exclusion already existing to test it out.
When its complete the AV exclusions in Windows should looks similar to the partial screenshot below.
To view the exclusions, in Win 11 open ‘Virus & Threat Protection’ > Manage Settings > Under Exclusions chose ‘Add or remove exclusion’
